Cybersecurity - Data Privacy - IT Trends - Innovations
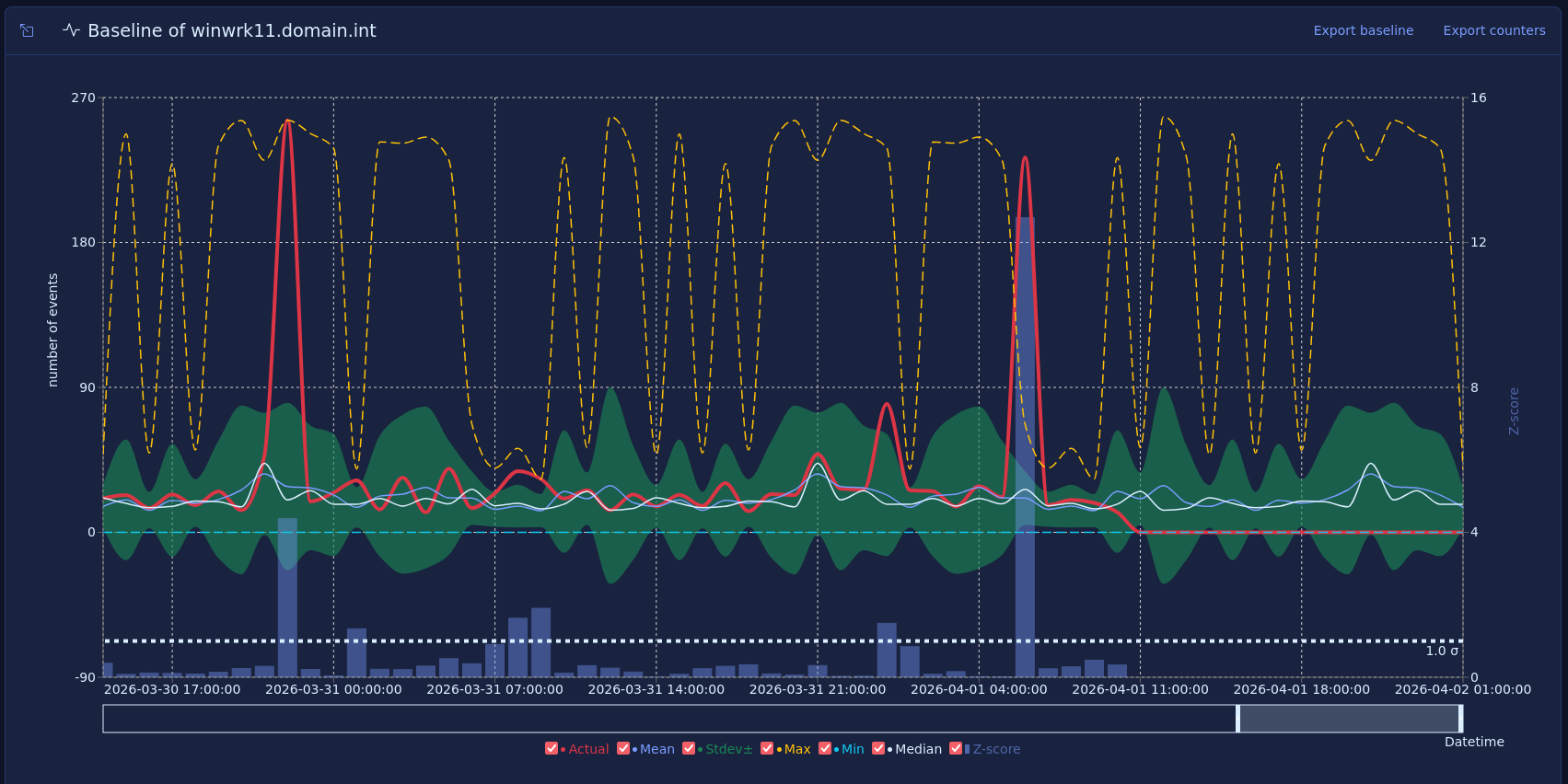
Vector baselines and host behavior
Most security monitoring focuses on what happened, such as a failed login, a new admin, or a suspicious process. That approach is useful, but many strong warning signs do not come from one event. They come from a change in how a host behaves over time.
Published on March 16, 2026
Building the Correlator #2: Window architecture
In the previous article, I described what the window correlator is good for, analyzing long series of data to gather security incidents and produce alerts. I also discussed the memory issue that comes with storing long series of data composed of events, which come to the application at a frequency of tens of thousands of events per second. The proposed solution is to store only relevant parts of the series, here called segments, in memory. Now, we'll take a look at the segments in more detail, so we know exactly what structures they are composed of.
Published on June 15, 2024
Building the Correlator #1: Analyzing long series of cybersecurity data with window correlation
In a cybersecurity system, there are usually tens of thousands of messages transmitted every second, each containing information about user behavior, device status, connection attempts, and other activities performed in a network infrastructure. These messages are called logs, and they are produced not only by the servers themselves, but by all kinds of applications running on those servers, as well as network devices such as firewalls.
Published on May 15, 2024

Log management for absolute beginners
New to log management and cybersecurity? Or, maybe you're already a pro, but you're looking for a way to explain log management to someone who is? Either way, you're in the right place.
Published on April 15, 2024

A beginner-friendly intro to the Correlator for effective cybersecurity detection
At TeskaLabs, we know that a cybersecurity system is only as effective as its ability to detect threats. That's why we developed a powerful tool that will prove essential in your arsenal: the Correlator.
Published on March 15, 2024

TeskaLabs LogMan.io: Microsoft Office 365 dashboards
Microsoft Office 365 is used daily by a large number of companies, businesses, and individuals. But only a few people know that Microsoft Office 365 provides very detailed data about who is working with them and how.
Published on May 15, 2022
How to enter the world of logs and cybersecurity.
What does it mean to log, create a corresponding dashboard and start writing JSON syntax? As I searched for answers to these questions and what were my first steps in tracing the world of cybersecurity.
Published on March 15, 2022
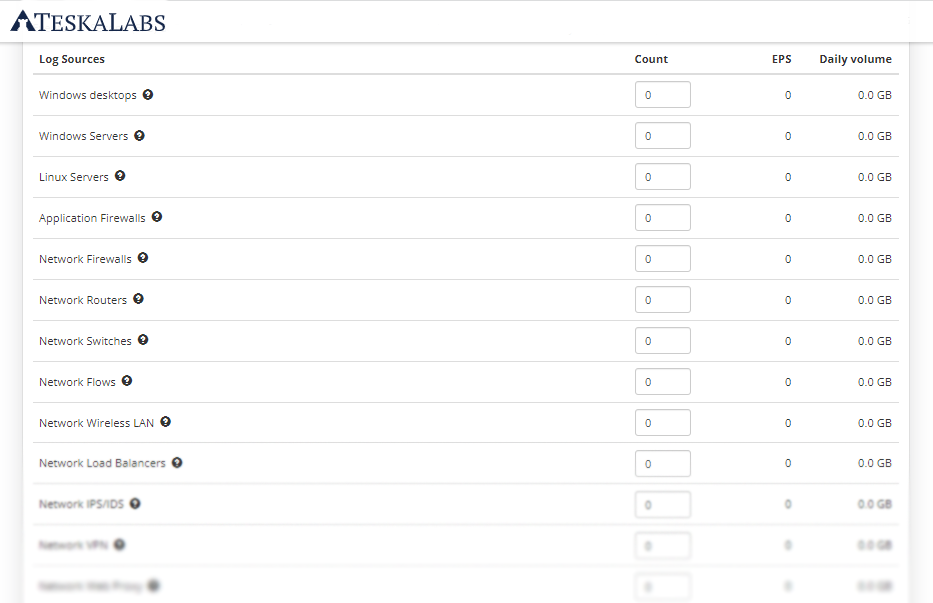
How big Log Management or SIEM solution does your organization need
Calculate size of IT infrastructure and how much EPS (Events Per Second) generates.
Published on December 15, 2021

Case Study - TeskaLabs SIEM for large Czech government organization
TeskaLabs delivered full-fledged SIEM solution for large Czech government organization with branches all over Czech Republic and need to process at least 20,000 EPS. The delivery was successfully completed on time and on budget.
Published on October 15, 2021
The 8th version of the European Certificate Trust List (ECTL) for C-ITS has been released
The Joint Research Centre of the European Commision (EC JRC) released the eight edition of the European Certificate Trust List (ECTL) used in Cooperative Intelligent Transport Systems (C-ITS). L0 ECTL v8 contains five new Root CA certificates and one re-keyed Root CA certificate. Three out of five newly inserted Root Certificates are installations that run on the TeskaLabs SeaCat PKI software for C-ITS.
press
automotive
c-its
v2x
security
Published on September 16, 2021

TeskaLabs delivers cybersecurity for nationwide C-ITS project in Czech Republic
TeskaLabs delivers Seacat PKI, public key infrastructure security technology, for newly emerging nationwide C-ITS project in Czech Republic.
press
automotive
c-its
v2x
security
Published on August 25, 2021

TeskaLabs SeaCat PKI for C-ITS delivered to CertiLab of Czech Technical University
TeskaLabs supplies the SeaCat PKI and the dedicated C-ITS security testing tool for CertiLab, laboratory for the development and testing of technologies for Cooperative Intelligent Transport Systems (C-ITS).
press
automotive
c-its
v2x
security
Published on July 07, 2021
TeskaLabs SeaCat PKI deployment for NordicWay C-ITS pilot in Norway
In many respects, today's motor vehicles function as connected devices. With this in consideration, joint EU initiatives have broadened the impact of Cooperative Intelligent Transport Systems (C-ITS) to include more expanded connections, including road infrastructure. This enhanced connectivity is expected to result in significant improvements to both road safety and traffic efficiency.
press
automotive
c-its
v2x
security
Published on June 15, 2021
C-ITS: The European Commission is updating the list of the Root Certificates
23rd April 2021 marks the release of the fifth edition of the European Certificate Trust List (ECTL). This was released by the Joint Research Centre of the European Commission (EC JRC), and is used in Cooperative Intelligent Transport Systems (C-ITS). It is otherwise known as the L0 edition release, intended for use primarily in test and pilot deployments. Currently these activities are primarily European and focus on fields such as intelligent cars and road infrastructure.
press
automotive
c-its
v2x
security
Published on May 06, 2021
Five Ways AI And Machine Learning Can Enhance Cybersecurity Strategy
Artificial Intelligence (AI) and its essential component machine learning are causing a stir in practically every industry from marketing to education. It’s no wonder designers and tech developers are finding ways to use the benefits of automated technologies to improve cybersecurity infrastructure and defend against increasingly complex and numerous cyber threats.
Published on June 24, 2020

Why Hackers Target Small Business Websites 5 Tips to Stop them
With the rise of online businesses, so does the hacking community. Many talented people with barbarous intentions from across the world develops systems with one intention in mind, to harm and attack websites and ruin the day for most entrepreneurs.
Published on October 15, 2019

Making Automated Mobility Safe
Autonomous vehicles are still working their way into the modern automotive marketplace. However, they are growing more common each year. Many agree, this is an innovative change, and it’s estimated that there will be more autonomous vehicles on the road in the coming years.
Published on July 15, 2019

Connected Vehicles: Are we ready?
Connected vehicles that talk to each other, increase road safety, and rely on automation all seem like a plot from a sci-fi movie. When does the robot takeover come in? As outlandish as all of this might seem, we’re closer than ever to connected vehicles being the new normal on our roadways. In fact, by 2025, every car on the road is expected to be connected in some way, shape, or form.
Published on June 15, 2019

The Most Prevalent Wordpress Security Myths
WordPress web development may not seem like a challenging task. Since this platform has been in existence, a wide range of Web developers have handled projects of this nature. However, the top web development companies are not always aware of the issues and problems that take place when it comes to security.
Published on April 15, 2019

9 Usefull basics to deal with the cybersecurity
When it comes to dealing with the modern business, cyber security is more than an afterthought. Poor security standards will cost you more than just business, too; it could cost your reputation, or even your ability to trade.
Published on March 10, 2019

Future of the Automotive Mobility and Data Security
Mobility has always been at the cutting edge of human innovation and technological advancement. This is unlikely to change in the foreseeable future. Already, mobility as we know it is seeing significant disruption thanks to the entry of nontraditional players who are leveraging the power of computing devices and the Internet. But few things are likely to have a bigger impact on mobility than the enormous volumes of data that will be generated as a result.
Published on February 10, 2019

White box vs. Black box penetration testing
When it comes to hacking, there are many technical aspects that can be difficult to grasp without an extensive background in the field. One of the most common sources of confusion is the comparison between black box penetration testing and white box penetration testing.
Published on January 15, 2019

TeskaLabs Ltd was Innovate UK Funding Competition Winner in 2018
While every company is drawn to answering big questions and making new discoveries, not everyone is excited about how to get there: securing money for growth. Even with billions spent on business research and development around the world, there is considerable competition for funds.
Published on November 01, 2018

Google has introduced new rules about how mobile app developers and companies deal with customer impact on apps across the board. What is it?
The new regulations call for increased transparency with regards to how apps make use of customer data. Developers need to ensure that the way they handle user data - from how they collect it to what it might be used for - is perfectly clear to all users. In Google’s words, developers must “limit the use of the data to the description in the disclosure”. In layman’s terms, this means that data use and privacy policies need to be clearly visible on app descriptions in the Google Play store, and not simply within the app itself.
Published on October 10, 2017

Industrial IoT Security: Cyber Security Implications for IT-OT Convergence
In June 2017, two information security firms researching the 2016 hack of the electricity grid in Ukraine announced that they had identified the malicious code used to shut down power stations and leave thousands of households and businesses in darkness for several hours. The malware used to target the Kiev power grid has been named Industroyer, and it serves as a sobering reminder about the dangers faced by the Industrial Internet of Things (IIoT).
Published on September 05, 2017

How TeskaLabs Helped O2 Improve Customer Satisfaction of eKasa Point-of-Sale (POS), the Most Successful POS Product / Mobile Cash Register on the Czech Market
In 2016 the Czech government introduced a new law that required businesses to report their sales and provide Electronic Evidence of Sales (EET). This law calls for the adoption of a more modern point-of-sale system that enables businesses to meet regulatory requirements set forth under this law. During the next two years, the law will gradually impact more than three hundred thousand companies in the Czech Republic. O2, the largest integrated telecommunications provider in the Czech market, observed that many would need help complying with this law, maintaining data security and demanding excellent customer support.
Published on August 08, 2017

Binary distributions of OpenSSL static libraries
The official source of OpenSSL software is the OpenSSL website. One can download OpenSSL source codes archives and compile them for a given platform. The compilation work can sometimes be quite tedious, especially for exotic platforms. We, at TeskaLabs, set up this page because we frequently compile OpenSSL for various platforms for our internal purposes and this may save some time to other developers.
development
android
windows
ios
security
Published on July 20, 2017

Online Fraud Is Increasing - Is Business Intelligence the Answer?
With the year on year rise in ecommerce, there is a corresponding rise in online fraud - in fact, according to Financial Fraud Action UK, this type of activity had increased by a quarter to £399.5 million in the first half of 2016. The most recent manifestation of this is the concept of “testing” - this is where the criminals try small purchases to check the validity of card details, before moving in for the kill.
Published on July 04, 2017

How TeskaLabs Helps You Operate SCADA Systems Securely and Comply with Security Laws
Cyberspace does not have boundaries. The internet is a truly international community, and it takes just milliseconds to reach a data source on a whole different continent. The internet is therefore an open arena for cyberattacks from across the world, where anyone can try to break their way into someone else’s data. We can see this daily in the news or on the specialized ICT news servers- the attacks never stop.
Published on June 06, 2017

5 Cyber Threats eCommerce Websites Should Watch Out For
There are innumerable advantages to eCommerce. Businesses can make sales outside of business hours; they can reach customers over their own personal social media pages, and take advantage of people being more inclined to spend while they’re on the couch with a glass of wine rather than harassed in the changing room of a crowded store. However, with all of these advantages, there are also some inherent threats that could annihilate a business’ reputation.
Published on May 02, 2017

Who is Responsible for Securing the Connected Car?
The automotive industry recently witnessed several cases of cyber-hacking that made driving connected cars dangerous if not impossible. Companies like Jeep, Volkswagen, and Tesla all have recently dealt with cases of hackers taking over cars and stopping them while the cars were in use as well as stealing customers' Social Security numbers, financial details, and other sensitive information.
Published on April 04, 2017

Why You Need Security Audit for Your Point-of-Sale (POS) System
It’s clear that POS systems are a source of important and valuable data, and have the power to either speed up the progress or to stop the development of a company, depending on whether or not they are used. POS data is a business asset. Despite this vital importance, such an asset is not afforded the protection it deserves.
Published on March 07, 2017

How DDoS Attacks Can Sink Your Business
Distributed Denial of Service (DDoS) is a form of cyberattack which makes the target internet service inaccessible. “Distributed” refers to the fact that the attack comes from multiple sources, to have a bigger impact on the target, as it cannot cope with such a large amount of traffic. In recent years, DDoS attacks have become more and more complex, with many combinations of different attach approaches being used.
Published on February 07, 2017

4 Common Mobile Point of Sale (POS) Security Issues Affecting Retailers That POS Providers Need to Act On
As mobile point-of-sale applications and systems are picking up speed at retailers around the world replacing traditional one, they become appealing targets for cybercriminals allured by the amount of consumer data entered in POS systems whether through unauthorized access, mobile malware or hacking the backend.
Published on January 03, 2017

SeaCat and OpenSSL Heartbleed Bug
After almost two and a half year we hope that the Heartbleed remains in the past. It is not true, unfortunately. Now we have proof that a security vulnerability remains with us for a long time, maybe almost forever even when there exist patches and fixes. The Internet is a battlefield among the good, the bad, and the ugly. Who has better attacking or defending technology wins.
Published on December 20, 2016

The Real Impacts of General Data Protection Regulation (GDPR) to EU Companies That Operate Mobile Applications
The General Data Protection Regulation (GDPR) is a new EU regulation aimed at protecting the personal data of EU citizens. Because of the broad definition of “personal data”, GDRP impacts almost every EU company, as well as non-EU companies that exchange data with them. The regulation takes effect in May 2018, which is still a long way in the future, but the complex requirements mean that companies need to start planning and taking action now.
Published on December 06, 2016
Key Areas and Best Practices to Focus for Mobile API Security
With APIs (Application Programming Interfaces) becoming a crucial factor in any web or mobile application, security feels more like a journey than a destination. Of all the constituents that encompass an application, API gateway offers easy access points for a hacker to break in and steal your data. A single error in API can cause immense problems for any organization using your API.
Published on November 22, 2016

Android Nougat: Google OS' Tightest Security Yet
Officially released a month ago, the latest Google mobile OS version has made a few major adjustments, particularly in its security features. The search giant has improved the security in the Android Nougat (or also known as Android N) from strengthening the Android itself to some tools that helps developers to keep things as it is while users install apps.
Published on November 15, 2016

5 Things You Need To Know About Securing Your Game App
The game industry is constantly evolving and growing on a rapid scale by each passing day. A significant part of this industry is mobile gaming. With huge advancements in mobile device technologies, gaming apps are on a high demand and so is their supply. One of the major reason behind this are the developers who are splurging millions of dollars in their time to market strategies. In all of this, the security of gaming apps takes a backseat, overlooked by developers in a haste a to launch their product before their respective competitors.
Published on November 08, 2016

Want to Be a “Man in the Middle” of a Mobile Communication? It’s Easier Than You Think
Mobile are everywhere nowadays and a central part of almost everyone's lives. In fact, we are using them for everything - both for personal and business purposes. From streaming media entertains us on our way to work, to chatting with friends and family, to sending emails at work - mobiles are now effectively computers on the go. According to a study from Cisco, we are using mobile access more and more. And this trend will continue well into the future.
Published on October 25, 2016

80% of Androids Are Vulnerable to Linux TCP Flaw. But I Don’t Care!
Researchers from the University of California, Riverside, and the U.S. Army Research Laboratory have found an off-path TCP vulnerability [1] that affects more than 80% of Android mobile devices. Unlike a Man-in-The-Middle attack, you don't need to be in the middle of the communication to get hacked - all attackers need to know is who you communicate with.
Published on October 11, 2016

What Is Mobile Application Containerization or Wrapper, and Why It Needs to Go?
Containerization is an alternative for full machine virtualization. You probably know well-known containerization technology from Docker or Rocket. However, this article addresses the pros and cons of mobile “containerization” or wrapper used to isolate the mobile app from the mobile operating system or other applications installed on the same device. These type of “containerization” work in a different way.
Published on September 27, 2016

Is There A Network Protocol for Your Mobile Apps That Offers A Higher Security Level While Consuming Less Bandwidth Than HTTPS? Yes, There Is
For mobile apps or websites that don’t have logins, forms or features to extract data, you don’t need secure access. For banking websites, mobile apps and mobile banking services, without a doubt, secure communication is a must. But nothing is ever black and white.
Published on September 13, 2016

How to Teach Your Kids to Safely Play Pokemon GO
This summer something strange has occurred in my household. Suddenly, all of my children ranging in age from 9 to 18 are willingly piling into our van the minute I mention driving anywhere- even to the grocery store. And it’s not my company or the possibility of picking out this week’s cereal they are seeking. No, they are merely wanting a ride to aid them on their hunt for elusive Pokémon.
Published on August 30, 2016

Custom Made vs. Off-The-Shelf Mobile Apps – The Issue of Security
In October 2015, Blakely Thomas-Aguilar did a great article on mobile security statistics on the VMware AirWatch blog that can and will send shivers down your spine. For example, she found that there was an increase of 18% in the number of Android vulnerabilities between 2011 and 2015.
Published on July 26, 2016

Are You Ready for The New European General Data Protection (GDPR) Law?
A new EU regulation, European General Data Protection Regulation (GDPR) has been proposed to improve the data protection of individuals. This regulation is the subsequent to the 1995 directive. It was agreed on 17 December 2015 and its implementation starts from 2018.
Published on July 12, 2016

You Can Build Apps for the Apple TV, But Do You Know How to Do It Securely?
Apple will want to dominate the market for TV apps. To achieve this objective, it’s understandable that Apple makes it easy for app developers to create apps and games for the Apple TV platform using tvOS and profit from them just as they have already done so for the iPhone and iPad devices. Developers can leverage similar frameworks and technologies since tvOS is just a modified version of the iOS. They can even retrofit the apps that were previously developed for iOS to support the Apple TV’s tvOS.
Published on June 29, 2016

We Know Why 85% of Mobile Apps Suck in Security. Do You?
In just the past 12 months, we’ve come across 100 mobile app projects at different phases. We’ve had conversations with more than 300 professionals active in the enterprise mobility space. We asked questions and uncovered the underlying problem that caused the current miserable state of mobile application security. It sucks. The answer doesn’t lie in technology but in us.
Published on May 19, 2016

Security Is Driving the Adoption of Connected Cars
What seems to be a Sci-Fi movie with “talking” vehicles and “flying” machines has now become a reality. Automotive companies, seeing huge opportunity and wanting to entice their customers, are rushing to produce more car features so drivers can avoid traffic congestion, plan the next route, check the status of the car, find an available parking space, request for road assistance, or notify friends/family members/business contacts of news.
Published on May 10, 2016

Why Is Data Encryption Necessary even in Private Networks?
Securing data transferred between different endpoints is important not only through public networks but also in private networks. The data has to be protected if it is business critical or if modification or interception leads to a security incident with a high business impact.
Published on May 03, 2016

OpenSSL DROWN Vulnerability Affects Millions of HTTPS Websites and Software Supporting SSLv2 (CVE-2016-0800)
DROWN is caused by legacy OpenSSL SSLv2 protocol, known to have many deficiencies. Security experts have recommended to turn it off, but apparently many servers still support it because disabling SSLv2 requires non-default reconfiguration of the SSL cryptographic settings which is not easy for common IT people who have limited security knowledge and don’t know the location to disable this protocol and the way to disable it.
Published on April 12, 2016

Better Late Than Never - WhatsApp Is Using End-to-End Encryption – Finally!
Can you imagine leaving your house without locking the main door while you are out? I guess not. Locking the door is a routine that we're doing automatically, so why there is so much noise about the latest update from WhatsApp that seems like the company has just reinvented communication encryption?
Published on April 07, 2016
Application Security Issues for HTML5-based Mobile Apps
HTML is no longer restricted to just websites. With its latest edition, HTML5, the markup language family has now become a popular choice for mobile applications. After gathering the relevant data and researching, Gartner predicted two things; firstly, HTML5 would be the most commonly used language for mobile applications in 2015 and secondly, HTML5-based hybrid mobile app using technologies such as PhoneGap, Codova or React Native reach up to be 50% of all mobile apps 2016.
Published on March 01, 2016

7 Reasons Why Mobile App Security Testing Is Crucial for Enterprises
Gartner reports that by the end of 2015, 75% of mobile apps will fail basic security tests. Over 2/3 of large enterprises have been breached via mobile applications. Each security breach up costs up to $3 million/year. The estimated annual cost of mobile cyber breaches is around $50 billion, globally and increasing.
Published on January 12, 2016

The Security Vulnerability That Puts Millions of Application Backends at Risk. Yours Included
FoxGlove Security researchers published a serious vulnerability that can put millions of application backend, including mobile backend, at risk. Mobile applications use the same web-app technology for their backends, thus suffer the same vulnerability. Mobile application servers are inherently insecure because they consist of extensive stacks of software. Each piece can contain risky zero-day vulnerabilities.
Published on December 15, 2015

The Two Real Challenges of the Internet of Things
Every week there is a new connected device on the market. A few days ago Tag Heuer launched its smartwatch with Google, and last week I saw a €39 sleep tracker in my supermarket plaster section. Tech conferences are buzzing about the Internet of Things (Consumer Electronics Show 2015, Pioneers Festival 2015).
Published on November 24, 2015

The TalkTalk Hack: What You Need to Know
TalkTalk, one of the largest providers of broadband and phone service in the UK, has recently admitted to being the victim of a large cyberattack. For those in the United States or in another country where TalkTalk’s influence isn’t as widespread, it could be considered on the same level as a Verizon or an AT&T data breach.
Published on November 10, 2015

The Top 5 Mobile Application Security Issues You Need to Address When Developing Mobile Applications
Most recently, a lot of established companies like Snapchat, Starbucks, Target, Home Depot, etc. have been through a PR disaster. Do you know why? Simply because some attackers out there found flaws in their mobile apps and could exploit them. In fact, by the end of this year, 75% of mobile apps will fail basic security tests.
Published on November 03, 2015

Understanding the Importance and Value of Backend Security
We know that backend security is important, but what exactly constitutes the “backend?” To put it simply, the backend is the portion of a website, web application, or mobile application that exists behind the scenes. By contrast, the “frontend” of an application is everything that the user interacts with. This includes design features in the website or application, links, transactions, images, content, and others.
Published on October 06, 2015

Develop Enterprise Mobile Apps? Turn Application Security into Profit instead of Cost
More than 3/4 of enterprises have experienced mobile security breaches. These breaches cost larger enterprises approximately 3 million dollars. One reason is the build cost to properly implement mobile application security measures.
Published on September 29, 2015

Security Architect Jiri Kohout: It's up to Us to Define How Secure The Internet Will Be
The security of connected applications, IoT, or mobile platforms, is based not only on secure development, but also on widespread knowledge about info security. Every user should have minimum knowledge about security. Every public tender should demand security of the final product or service.
Published on September 15, 2015

Security Researcher Filip Chytry: Online Security Is an Unattractive Topic - until People Get Hacked
I studied at Applied Cybernetics school and worked on various fields: robotics, networks and programming. There I got curious about security and became increasingly passionate about the industry, trying to learn more about cyber crime and attempting to hack into my classmates‘ computers for fun.
Published on August 20, 2015

Hacking Team Getting Hacked - In Whom We “Trust”?
The hack on the Italian-based firm Hacking Team revealed that exploiting is not just done by black hats and bad hackers but can be committed by a legitimate company. A dump of 400 gigabits email revealed that the company was involved in zero-day exploits.
Published on August 04, 2015
What Happens When Hackers Hijack Your Car ... While You’re in It
What do Chrysler Jeeps, GM cars, and Tesla Model S have in common? They are now becoming giant smartphones traveling on a highway. They all have serious security vulnerabilities and can be hacked!
Published on August 04, 2015

Apple's Zero-Day Security Flaws on iOS, OS X Let Hackers Steal User Passwords
To show Apple a flaw in their environment, a team of University researchers created a malware app and uploaded it to the App Store. This malware can steal passwords from installed apps, email clients, and Google's Chrome web browser. By exploiting this flaw, hackers can bypass the App Store security check using this hacking app.
Published on July 28, 2015

Connecting the Unconnected. Securing the Internet of Things (IoT)
The Internet of Things (IoT) has unleashed new trends, and things are now labeled Smart-X (X = things). We can now connect the unconnected like cow or Barbie doll. But anything that can be connected can be hacked.
Published on July 14, 2015

Snap to It: Mobile Secure Gateway Is In Your Future
The enterprise world is changing. In the past, enterprises built their IT infrastructure as isolated data fortresses and did everything they could to prevent outsiders from accessing their data. But now they need to open that fortress to allow communication via mobile technologies. And this hole is where hackers strike.
Published on July 07, 2015

5 Reasons Why Security Matters When You Want to Go Mobile
Security is an essential part of today’s modern world, especially with the rise of computers and mobile devices. No one questions whether data centers, servers, and computers should be secure, so why are there so many questions about mobile security? Mobile devices face the same security threats and are, sometimes more susceptible to them. It is time to make mobile security a priority.
Published on June 23, 2015

Look Who's Talking! Privacy and Security Concerns Over The New Hi-tech Barbie
Our Business Development Manager, Pavel Enderle, had an interview with CT24 TV, a Czech television channel, to discuss cloud security regarding the new Barbie product, Hello Barbie. This Barbie can talk to children by using ToyTalk’s system to analyze the child’s speech and produce relevant responses.
Published on June 09, 2015

Security Issues in Nissan’s Mobile App, NissanConnect, Could Potentially Put Users’ Data at Risk
As technology continues to advance, cars are increasingly becoming integrated into our mobile devices. Automotive brands are now releasing mobile apps, allowing users to connect their music streaming services, social networks, and search engines into the car’s system. One app that I’d like to highlight is NissanConnect, a mobile application from Nissan.
Published on May 28, 2015

MazelTov and the Russian Underground Have It Going for Your Android Devices. But Not for Good Reasons
The Internet has been a good place for individuals and businesses. However, it's fast-becoming a leading medium for criminals in this cyber war against people like you and I. One example is the Russian underground that sell anything to do with cyber crime. On their websites, you can find any type of Trojans, exploits, rootkits and fake documents.
Published on May 19, 2015

A Warning about Zero-Day Vulnerability
A zero-day, also called zero-hour, vulnerability is a security flaw in the code that cyber criminal can use to access your network. Zero-day attacks call for new technologies built from the ground up for today’s advanced threat landscape. There is no known fix, and by the time hackers attack, the damage is already done
Published on May 12, 2015

How to Win in the Enterprise Mobility Market
At the Dublin Web Summit, I had many interesting chats with people who developed mobile apps for enterprises and large companies. Despite their differences, most had the same mindset regarding the security of their mobile apps and the backends. 'It's as secure as the infrastructure at our customers.' Is it? Let's find out.
Published on April 21, 2015

Why Developers Are Boosting Up Their Mobile Application Security?
Mobile application security is a significant issue for developers. Most try their best to make mobile apps secure and safe for their users. Here are some of the other reasons why developers are boosting up their mobile application security.
Published on April 14, 2015

Situations Where Mobile App Security Best Practices is Necessary
The use of mobile app security best practices has become a necessity as app development and mobile usage continue to grow. These practices are needed to improve consumer protection, trust, and regulatory compliance.
Published on March 24, 2015

SQL Injection - Are Developers to Blame for Data Security Breaches?
Of course, this is a bold statement, but for those who deal with security issues from mobile applications, they can pinpoint where the flaw occurred with developers not taking security into account when developing mobile apps. Security takes the back seat to app functionality and remains as second thought.
Published on March 07, 2015

The Golden Age of Black Hats
I experienced a precious moment, discovering the cause which contributed to today's dire state of mobile application security. App developers think that if their apps do not deal with money, they should not have to care about app security. Is it true?
Published on February 24, 2015

Distributed-Denial-of-Service (DDoS) Disrupted Gaming Industry During the Holiday - What You Need to Know
During the Christmas holiday, the Xbox and PlayStation networks at Sony and Microsoft game websites were taken down by a group of hackers called Lizard squad. This attack put thousands of users out of game playing. What a bummer huh? Originally, the FBI blamed the North Koreans for taking down the network--that is another story, but had since revised their assessment when the Lizard squad claimed responsibility for the attack.
Published on January 27, 2015

Android: The One That Gets The All the Attention - Developers, Hackers and YOU
Android is considered one of the best operating systems used in smart phones. This operating system is backed by Google, the number one search engine. The Google Play has become an obsession now, enjoying the biggest number of smart phone apps. Many of them are absolutely free. But what if we tell you that Android is the easiest operating system to hack and even customized apps such as Gmail can be hacked. Recently it was checked and confirmed that Gmail is one of the top endangered apps, which can be hacked very easily.
Published on January 20, 2015

The World of Mobile Apps Is Not As Secure As You Think
Mobile app startup companies are notorious for cutting corners. One of the first things that is cut is security. After all, they have the big guys like Comcast, AT&T, and Verizon to protect mobile users, right? Wrong! All the way down the line. TechCrunch's article about security for mobile devices is an interesting theory on the state of security on the Internet. Although, they do hit the mark in the article about how companies fix the problem after the fact of the security breach.
Published on January 13, 2015

Having Fun with Your Android Apps? So Do Cyber Criminals
You love your Android phone and you love to go to the Play Store and download exciting new apps. You have also been through the Crazy Birds obsession and the Candi Crush mania. But do you know that your Android phone is not secured against the smartest of breaches: mobile app hackers. Before we go ahead and explain the intensity of this threat to mobile apps, especially Android apps, let’s have a look at the facts and figures!
Published on January 05, 2015

Business Intelligence and Mobile App Security
We are a security Cat, specializing in mobile application security. You know that. In the last couple of months, we happened to stumble onto another tech domain: Business Intelligence (BI).
business-intelligence
security
Published on December 26, 2014