
What Happens When Hackers Hijack Your Car ... While You’re in It! And What to Do about It?
What do Chrysler Jeeps, GM cars, and Tesla Model S have in common other than being smart?
They all have security vulnerabilities, and they can be hacked!
Why? Because our cars are now parts of a popular trend in which things are smart and interconnected. Our cars have turned into giant smartphones traveling on the highway.
Once the car becomes a device, a computer system, or a mobile phone, it is susceptible to hacking and security attacks like the rest of our digital equipments.
Breaking story about Chrysler Cherokee Jeep
The Chrysler Cherokee Jeep was the first -- “Hackers Kill A Jeep Remotely from the Highway - with me in it” by Andy Greenberg. This story details a hacking attempt into Greenberg’s car, rendering him completely helpless. All Greenberg could do was sit and wait. [Wired]
Two security experts, Charlie Miller and Chris Valasek, devised a hacking technique, a zero-day exploit, that gives attackers wireless control, via the Internet, to any of the thousands of vehicles on or off the road. This exploit can send commands to the Jeep's entertainment system, taking complete control of the jeep including dashboard functions, steering, brakes, and the transmission. And they can do from way across the country.
As you know, you won't be able to control the car, accelerate or brake it once the transmission is cut. Greenberg writes, di“The most disturbing maneuver came when they cut the Jeep’s brakes, leaving me frantically pumping the pedal as the 2-ton SUV slid uncontrollably into a ditch.”
Isn't it not bad enough dealing with existing hijacking incidents like physical break-ins and car accidents? Now, you have to worry about cyber hackers “digitally breaking in” and remotely taking control of your car from across town or the country.
Anybody, with enough skills and bad intention, can carjack from their computers. Hackers can track the car’s every move by tracking its “GPS coordinates, measure its speed, and even drop pins on a map to trace its route.”
VIDEO: Hackers Remotely Kill a Jeep on the Highway—With Me in It
Because there is an app for that
The indirect culprit is Uconnect, “an Internet-connected computer feature in hundreds of thousands of Fiat, Chrysler cars, SUVs, and trucks, controls the vehicle’s entertainment and navigation center, enables phone calls, and even offers a Wi-Fi hotspot.”Uconnect’s cellular connection also lets anyone who "knows the car’s IP address gain access from anywhere in the country," said the security researcher Miller.
Wait until you hear this! The security researchers decided to publish most of these hacks online. Bad hackers can use the same technique to hack into Chrysler or other connected cars. They can actively and aggressively make hacking attacks even easier and faster.
General Motors: Having my OwnStar
Meanwhile, another security researcher, Los Angeles-based Samy Kamkar, developed a device that can “find, unlock, and remote start General Motors cars equipped with OnStar.” [Arstechnica]
The hack, which is based on an exploit of OnStar's mobile software communications channel, exposes the credentials of the car's owner when it intercepts communications with OnStar's service.
The OwnStar device can detect nearby users of the OnStar RemoteLink application on a mobile phone and can then inject packets into the communication stream to the phone, getting it to give up additional information about the user's credentials. Those credentials can then be used to gain access to the vehicle's OnStar account and the full functionality of the OnStar RemoteLink app.
Tesla Model S: Everyone’s favorite is hackable
Chrysler and General Motors were not the only automakers to get "tested" by security researchers. The Tesla Model S electric car was also hacked into by researcher Kevin Mahaffey, who published his findings on the Lookout blog conveniently on the opening day of the 23rd annual Def Con hacking conference in Las Vegas. [IBTimes]
He found six vulnerabilities that allowed hackers to gain root privileges to the Model S' in-car entertainment systems. This gave hackers full control of the remote shut-off, remote lock and unlock the car, control the radio and screens, display any content on the screens (changing things like map displays and the speedometer), open and close the boot, and turn off the car systems.
These types of vulnerabilities allow hackers to exploit the NAV system in Tesla Model S, Chrysler, and General Motors cars.
Geez, at this rate what else hackers can do?
All three manufacturers have since provided patches to fix these vulnerabilities. However, at the moment, “Chrysler’s patch must be manually implemented via a USB stick or by a dealership mechanic.” Chrysler has also recalled 1.4 million cars after the Jeep hacking incident. The company has also blocked their wireless attack on Sprint’s network to protect vehicles with the vulnerable software.

What are recommended best practices?
SECURITY NEEDS TO BE CONSIDERED AS PART OF THE DESIGN AND DEVELOPMENT OF THE MOBILE APPLICATION
Applications have not been designed with security in mind, which is today’s common practice. Gartner predicts that by the end of 2015, 75% of mobile apps will fail basic security tests.
While Tesla Model S is hackable, security researchers praise Tesla’ software-first approach, having “key security features in place that minimized and contained the risk of the discovered vulnerabilities.” [Techradar]
ACKNOWLEDGE THAT SOFTWARE DEVELOPMENT AND SECURITY IMPLEMENTATION ARE NOT THE SAME
Software developers are not security experts. Developers focus on the coding, app features, and functionalities, not on implementing tedious security measures.
People in the security domain, researchers and hackers alike, are trained to see holes and loopholes. The researchers in the Jeep hack spent years to come up with these hacks. On the contrary, developers have to keep up with today's trend, build products fast and ship them out to the market as soon as possible, leaving little time for security testings.
That's why we build SeaCat Mobile Secure Gateway, a snap-on defensive armor for mobile applications, protecting data and application backends.
How SeaCat protects against these types of attacks to connected car
Because the car is accessible on the GSM network, hackers can get their hands on the car’s IP address and perform the hacks.
This is similar to how bad guys know where you live, follow you, and with some tricks, get into your house. But if you have a strong lock, you prevent them from getting in.
Let say hackers know the IP address of your car, track it, and attempt to break into it. However, they won’t be able to get in because the strong security protection and defensive armor that SeaCat provides for the car.
RESTRICT UNAUTHORIZED ACCESS
Obviously, hackers are not the people you want to get into your system. Since they do, there must be a problem with the authorization scheme. The owner of the application, the car manufacturer, chooses the person who can connect to the car. For example, the car owner has an authentication mechanism enforced by the car manufacturer.
The authorization scheme isn’t there. If there is, obviously, it’s not powerful enough. A strong authorization mechanism only allows you, the legitimate user, to have access or to grant whoever you choose to have access.
SeaCat strictly enforces a mutual authentication (mutual SSL), between the connected client and the server to prevent unauthorized parties from accessing the system.
PROTECT THE COMMUNICATION CHANNEL
As seen with the hack to GM OnStar application, hackers can “inject packets into the communication stream" to the phone, getting it to give up additional information about the user's credentials.
A SeaCat-enable application does not communicate with just anybody. Implementing the highest level of security protection, FIPS 140-2, military-grade encryption, you need to have a correct known cryptographic key to ensure only trusted parties can communicate such as the car manufacturer and the car owner.
Even if the communication stream is hijacked, and the hacker can see the transmitted data, they see only encrypted data but can’t understand it.
Hackers will see something like: “...QOiPacpN5vpwaY3YeIuUbQMsE99cEi7RTcLErfgVi/lutRhcVIHOy1pyV+9t1hEbU...”
We drew a simple diagram explaining the car hacking and how SeaCat can help prevent such attacks.

Still want a smart car?
Offensive hacking is fun and easy; that’s why many are doing it. There is even an underground market for selling hacking tools and services. Protecting and playing defense are harder and more boring. Miller says, “If it takes a year to introduce a new hackable feature, then it takes them four to five years to protect it.”
The auto industry can’t afford to take that long. “Given that my car can hurt me and my family,” Miller says, “I want to see that enlightenment happen in three to five years, especially since the consequences for failure are flesh and blood.”
SeaCat defensive armor is strong, yet easy to integrate with a smart car application and the car's backend; even a junior developer can do it correctly and quickly. It takes only a couple of hours, and you have strong security protection against these kinds of attacks.
"If consumers don't realize this is an issue, they should, and they should start complaining to carmakers. This might be the kind of software bug most likely to kill someone." ~ Charlie Miller
TeskaLabs are helping organizations to embrace mobile and Internet of Things without worrying about security risks and vulnerabilities. To learn about our security solutions and services, Contact us or tweet to us at @TeskaLabs.

Photo credit: Pixabay, Depositphotos
Most Recent Articles
You Might Be Interested in Reading These Articles
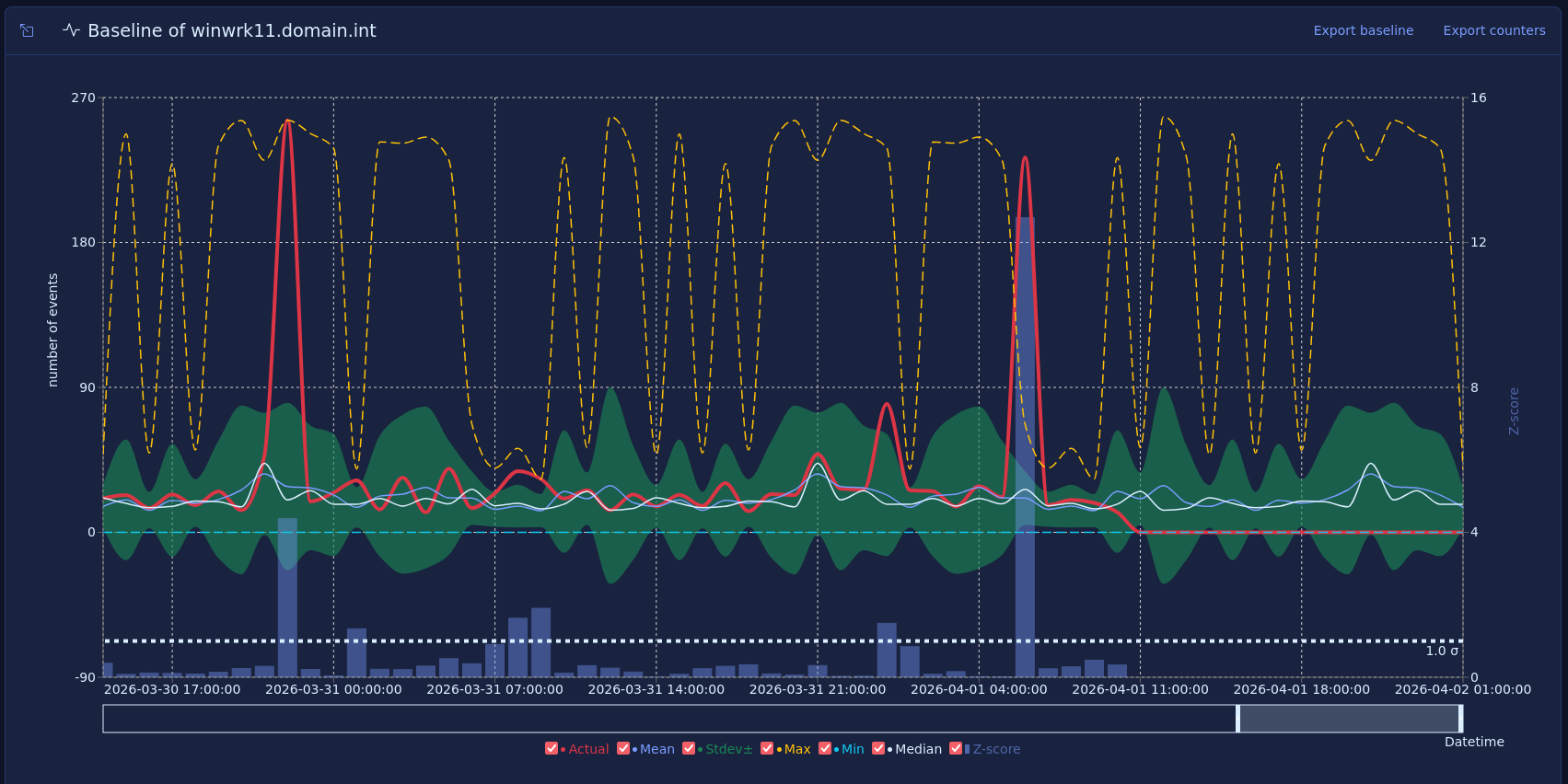
Vector baselines and host behavior
Most security monitoring focuses on what happened, such as a failed login, a new admin, or a suspicious process. That approach is useful, but many strong warning signs do not come from one event. They come from a change in how a host behaves over time.
Published on March 16, 2026

How DDoS Attacks Can Sink Your Business
Distributed Denial of Service (DDoS) is a form of cyberattack which makes the target internet service inaccessible. “Distributed” refers to the fact that the attack comes from multiple sources, to have a bigger impact on the target, as it cannot cope with such a large amount of traffic. In recent years, DDoS attacks have become more and more complex, with many combinations of different attach approaches being used.
Published on February 07, 2017

Having Fun with Your Android Apps? So Do Cyber Criminals
You love your Android phone and you love to go to the Play Store and download exciting new apps. You have also been through the Crazy Birds obsession and the Candi Crush mania. But do you know that your Android phone is not secured against the smartest of breaches: mobile app hackers. Before we go ahead and explain the intensity of this threat to mobile apps, especially Android apps, let’s have a look at the facts and figures!
Published on January 05, 2015
