
The Golden Age of Black Hats
A customer visit
I recently visited a customer’s industrial site. It was a huge warehouse with extensive value-added operations that included repackaging, rebranding, and spare parts among other things. The lead developer and I prepared for delivery of a mobile application that would support an existing process inside the warehouse.
Such warehouses usually have strict physical security requirements for admission. It includes getting securing an official authorization for admission, showing your bags, and adhering to a long checklist of DOs and DONTs. Once inside, your movement is further constrained by safety regulations and other rules protecting the valuable on-site assets since small incidents can disrupt plant production leading to incur significant costs for operators.
During my tour I saw all the physical procedures, various types of equipment checks, inventorization, and firmware upgrading stations that our new mobile application should support. We later sat at the desk and began discussing app features, such as the layout of each screen to be used by warehouse crew and the form fields that need to be there in addition to integrations with existing backend systems. I was positively surprised that the customer personally raised the question about information security for his mobile app. He commented that the app would communicate with the company’s servers over the Internet hence transmitted data could be eavesdropped and tampered.
A revelation
After we left the site and underwent several exit procedures with the site security officer, the lead developer turned to me and said that he didn’t understand why information security was important. I was completely stunned. “This is not a banking application,” he said. From his perspective, the data is not important in any way therefore "nobody is interested in them," and no special effort was needed to build the application in a secure way. He also said that he didn’t understand why there were such strict physical security requirements site.
When I finally recovered from my astonishment, I asked him why he thought we needed security only for banking apps and not others. He was unable to respond at first but later told me that the difference was probably about the money. Wow! I realized that I had experienced a precious moment discovering a psychological root which resulted in the state of weak mobile application security we have today. This kind of thinking is what causes a large number of breaches in mobile applications like those we’ve observed in the recent past and can foresee in the coming future.
Welcome to the golden age of the black hats
We’re talking about a lead developer who plays a very important role in the life cycle of an app. Yet, he makes a decision for his customer based on the belief that "It is not about money, thus we should not bother with security." The apps that he will develop will have a higher risk of being hacked and make a huge impact on his customers and end users. In this case, such risk will put the operational site in danger with its data center operating the backend of this mobile application together with the people associated with the operational cycle of the proposed application.
Do you put a lock on your front door?
Think about your house. You put a lock on the front door, not on your wallet. Of course you don't want someone to enter your house and steal your money, but you also want to prevent thieves from stealing your furniture and other possessions. You definitely don't want strangers to use your sofa when you are out. You implicitly expect that the architects and engineers who built your house had provided these fairly basic levels of security.
Unlike personal and physical security, cyber security (regarding networks, computers, applications) is more abstract thus harder for users to observe and take seriously. We take extreme care to protect our homes and feel some pain losing physical items. However we don’t mind doing major transactions on unsecure apps and risk losing much more than the value of the transaction. Mobile applications are not physical objects therefore 'unusual activities' are difficult or even impossible to be observed by the common user.
Why build secured mobile app at all?
Mobile app developers should not predict what kind of attacks will happen to their mobile applications. It is impossible to "outsmart" black hats — not because they are smarter but because they come from the future if I can put it that way. Hackers use attack vectors that are extremely sophisticated and unorthodox, many of which are automated, making it easier for them to devise attacks. One needs to have active control of their mobile application administrator functions as a tool to detect malicious communication. Finally, another way mobile operators and administrators can deal with attacks is in real-time while it is happening.
A mobile application can be exploited in many ways not only to steal data but also to tamper with its underlying functionality to interrupt business processes. Such an exploited mobile application backend can serve as a bridge into the data center to perform attacks on others applications that run from the same central location or network. A mobile app can be configured as a member of an illegal botnet that executes DDoS against others or participate in larger scale attacks. The ultimate responsibility lies in the hands of developers because only they can implement high levels of information security into mobile applications to protect their users against the dangerous world of today's Internet.
Until mobile application developers realize the severity of cyber security attacks and do something about it, we will continue living in the golden age of black hats.
~ Ales Teska
Most Recent Articles
You Might Be Interested in Reading These Articles
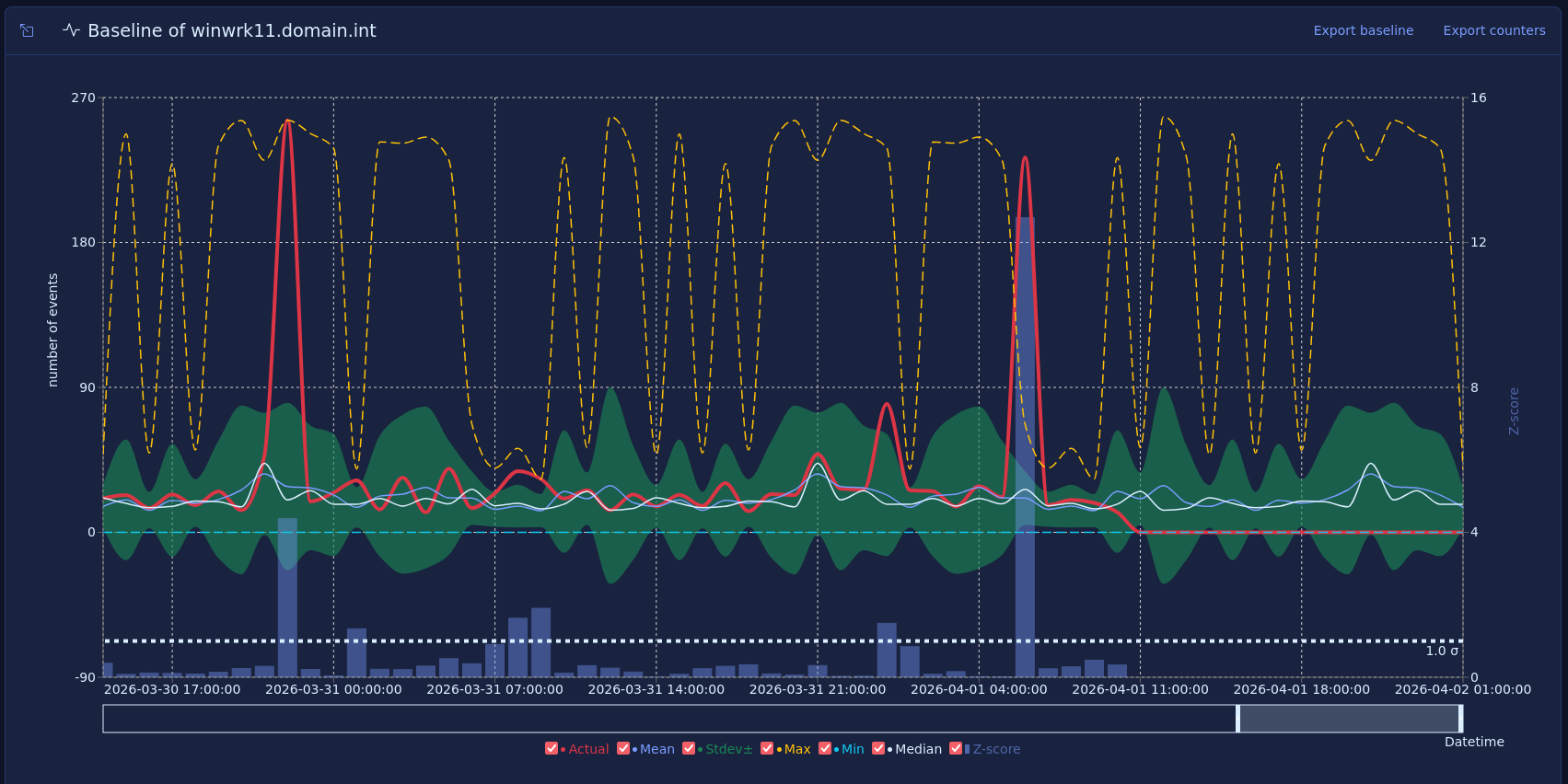
Vector baselines and host behavior
Most security monitoring focuses on what happened, such as a failed login, a new admin, or a suspicious process. That approach is useful, but many strong warning signs do not come from one event. They come from a change in how a host behaves over time.
Published on March 16, 2026
Building a private cloud on AMD Ryzen and Linux Containers
At our company, we develop our own software products that we offer to our clients and often also run ourselves. So far our company has operated its IT infrastructure — about 30 virtual servers—on a public cloud, specifically on MS Azure.
Published on July 01, 2018

7 Reasons Why Mobile App Security Testing Is Crucial for Enterprises
Gartner reports that by the end of 2015, 75% of mobile apps will fail basic security tests. Over 2/3 of large enterprises have been breached via mobile applications. Each security breach up costs up to $3 million/year. The estimated annual cost of mobile cyber breaches is around $50 billion, globally and increasing.
Published on January 12, 2016
