Situations Where Mobile App Security Best Practices is Necessary

The use of mobile app security best practices has become a necessity as mobile app development and mobile usage continue to grow. These practices are needed to improve consumer protection, trust, and regulatory compliance.
You should consider mobile app security as the lock on your house, with the mobile app being the house. Developers can build and live inside a house without any lock on their doors to save time and money. But because there is no home security, the house has a higher risk of being robbed. While having no security might have been acceptable in the past when the Internet was more of an academic place, there’s a need to use security best practices today.
Let’s go back to the house analogy. There are many ways in which you can install locks in your home. One method is to create your own lock, but it requires a lock of time and effort. And you need to maintain the lock forever. A strong lock will deter random strangers from trying to open it, and they will move to the next one with a weaker lock. But if someone deliberately selected your house to break in, the person will find a way. However, a strong lock will slow down the process. That’s why it is important to have good application security for your mobile apps to help deter scrupulous people from trying to steal information from you.
Developers need to use mobile app security best practices when dealing with any sensitive data, such as customer information, technical or business know-how, and strategic information.
Customer data include home addresses, credit cards, email addresses, and passwords. The information gathered by an app must be protected to gain the trust of the end users and protect them from identity theft as well.
Some mobile apps contain business know-how, such as a list of products or services. Take, for instance, industrial mobile apps that are used on forklifts and tractors in factories. They contain implementation procedures and other industrial secrets. There are mobile apps that contain strategic data, such as board decisions, Business Intelligence, and roadmaps. These are the types of apps that require mobile app security.
Mobile app developers must also consider mobile app security when working in certain industries, which have strict regulatory standards. Take, for instance, the health industry. Developers need to comply with the HIPAA. The military also has strict guidelines when it comes to security. Developers must know the standards to ensure that the mobile app complies with them.
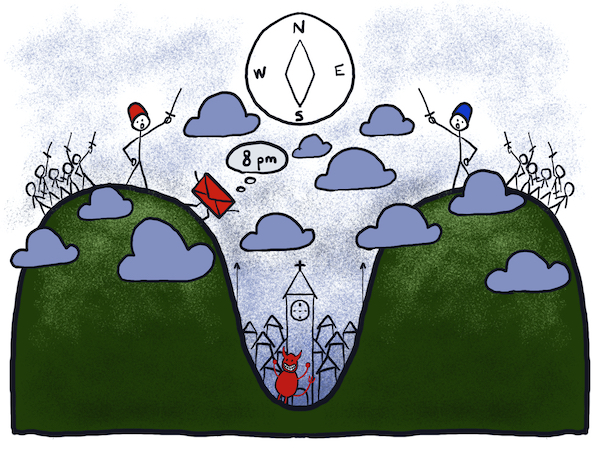
Mobile app security best practices are required to protect the business from competitors who resort to bad stuff to get an advantage. Distributed Denial-of-Service (DDoS) can be purchased these days, and an unscrupulous business owner could shut down one’s competitor. You can learn more the recent DDoS attacks that happened to Sony's game network last Christmas.
Security should be one of the priorities of app developers. Issues concerning security can’t be solved retrospectively. Plus, damage control can be very expensive. Just take a look at what happened to Sony. That’s why it is vital to consider using mobile app security best practices.
Request a FREE demo to know how you can add strong mobile app security right into your app development, differentiate yourself from other app developers and prove to your customers that you care about protecting their data.
Additional reading:
- Custom Made vs. Off-The-Shelf Mobile Apps – The Issue of Security
- You Can Build Apps for the Apple TV, But Do You Know How to Do It Securely?
- We Know Why 85% of Mobile Apps Suck in Security. Do You?
- 7 Reasons Why Testing the Security of Mobile Applications Is Crucial for Enterprises
- The Top 5 Mobile Application Security Issues You Need to Address When Developing Mobile Applications
- 5 Security Measures You Need To Know to Ensure the Security of Your Game App
Most Recent Articles
You Might Be Interested in Reading These Articles
Application Security Issues for HTML5-based Mobile Apps
HTML is no longer restricted to just websites. With its latest edition, HTML5, the markup language family has now become a popular choice for mobile applications. After gathering the relevant data and researching, Gartner predicted two things; firstly, HTML5 would be the most commonly used language for mobile applications in 2015 and secondly, HTML5-based hybrid mobile app using technologies such as PhoneGap, Codova or React Native reach up to be 50% of all mobile apps 2016.
Published on March 01, 2016
Don't worry, ASAB and the universe can be fixed
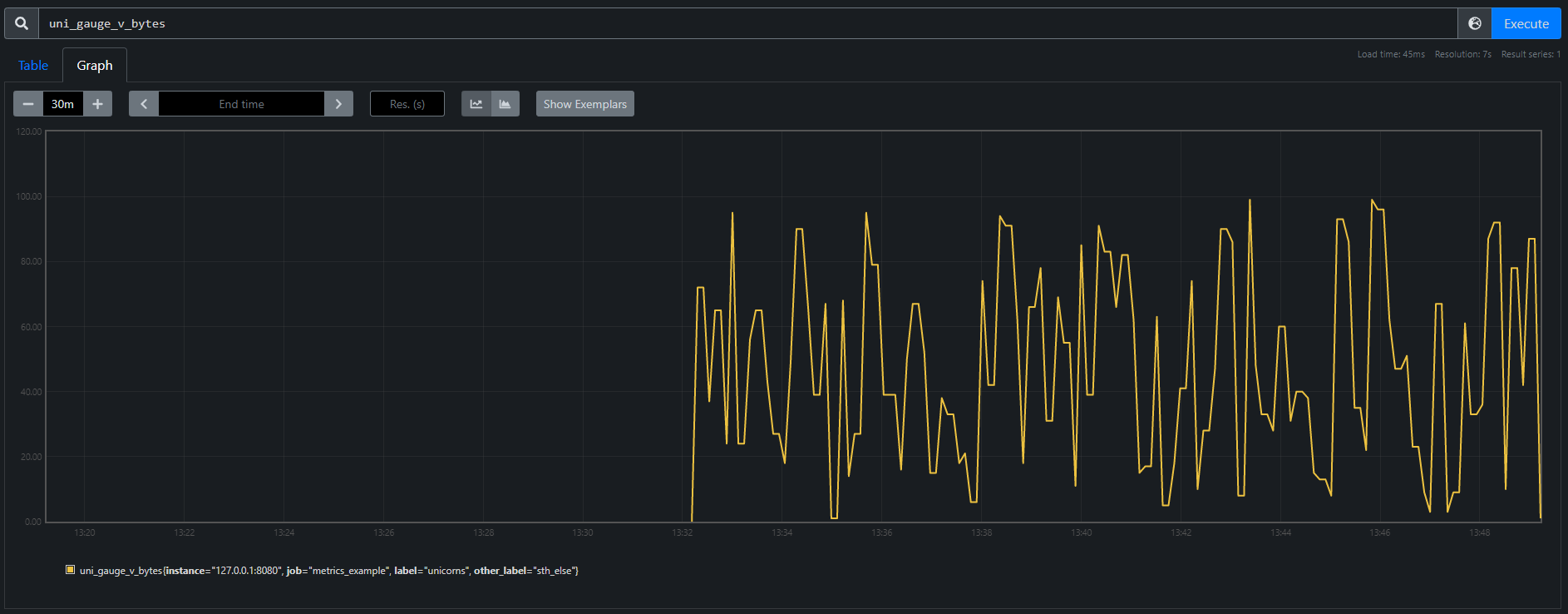
How do my first sprints in TeskaLabs look like? Sheer desperation quickly turns into feelings of illumination and euphoria. And back. I've also made a few new friends and learned a thing or two about flushing metrics. The digital adventure begins.
Published on February 15, 2022
From State Machine to Stateless Microservice
In my last blog post, I wrote about implementing a state machine inside a microservice I call Remote Control that will automate deployments of our products and monitor the cluster. Here I would like to describe how all this was wrong and why I had to rewrite the code completely.
Published on February 15, 2023