
How to Win in the Enterprise Mobility Market
Last year we exhibited SeaCat at the Web Summit in Dublin. On the second day I explored the venue visiting different exhibition booths in the Mobile Enterprise area and talking to the people there. Many of which have already developed mobile applications and other mobile solutions for enterprises and big companies. While these conversations were interesting, one thing in particular stood out. Regardless of the size, industry, or platform of the prospective client, they all had one thing in common — security, or lack thereof.
Surprisingly, the summit attendees had varying backgrounds ranging from developers, startups, and corporations yet they all responded similarly when I asked about the underlying security of their mobile apps and the back-ends. Their position is that they “are as secure as the infrastructure at our customers,” an alarming approach when discussing mobile applications that are more sensitive to security breaches than desktop applications.
CRM or BI data is traditionally accessed from office desktops. In this traditional environment the data remains within the internal network and is safe from threats. However, once CRM or BI data is accessed from mobile devices, it is beyond the protection of the enterprise network because the data is exposed to the outside internet.
Therefore, if you are an enterprise mobility vendor, your customers probably have not solved this particular security issue and rely on you as the developer to anticipate and respond to these threats. There is a potential risk of losing the client deal if you cannot show that have you aware of these threats. Even if you do get the deal, sooner or later you will be requested to fix the security part. That is not an ideal position to be in especially if you do not know to even solve the problem.
All hope is not lost. The solution lies in becoming educating on new security issues and establishing a protocol for addressing the same. Here are a few features you can employ to cover most basic security concerns as it relates to mobile applications and back-ends:
- Backend isolation
- Access control
- Automated client certificate request/renewal
- Protection of private key on mobile device
- Mutual SSL authentication
The above-referenced summit scenario is common given the rapid growth of mobile adoption. At the beginning of the mobile era, user experience and (visible) functionality were the only things that mattered. Today, security is becoming more crucial as more data breaches occur in organizations big and small. Naturally, enterprises try to avoid this kind of publicity so they are seeking developers who are knowledgeable about current security trends and requirements.
If you are in the mobile enterprise market, take security seriously. Do not rely solely on the skills and knowledge of mobile app developers because their underlying focus is on building a beautiful, functional application. Instead, use the best practices available and offer your customers not just functionality but also security.
Send us an email at support@teskalabs.com to get a free consulting session on your mobile solution and learn if there will be any potential risk to your data.
Photo credit Web Summit
Most Recent Articles
You Might Be Interested in Reading These Articles

5 Things to Look for in an Enterprise Mobile Development Platform Solution
Today many enteprises are looking to have their own mobile applications. With the right solution, you can build a mobile app that will fit your organization’s needs like a glove and be in the driver’s seat of the development.
Published on September 01, 2015
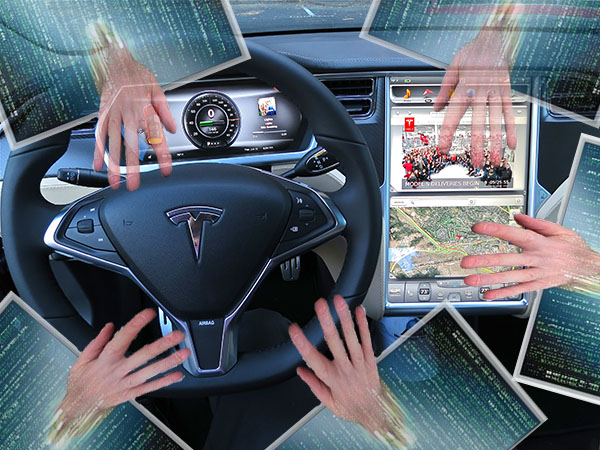
What Happens When Hackers Hijack Your Car ... While You’re in It
What do Chrysler Jeeps, GM cars, and Tesla Model S have in common? They are now becoming giant smartphones traveling on a highway. They all have serious security vulnerabilities and can be hacked!
Published on August 04, 2015

Google has introduced new rules about how mobile app developers and companies deal with customer impact on apps across the board. What is it?
The new regulations call for increased transparency with regards to how apps make use of customer data. Developers need to ensure that the way they handle user data - from how they collect it to what it might be used for - is perfectly clear to all users. In Google’s words, developers must “limit the use of the data to the description in the disclosure”. In layman’s terms, this means that data use and privacy policies need to be clearly visible on app descriptions in the Google Play store, and not simply within the app itself.
Published on October 10, 2017
