Benefits
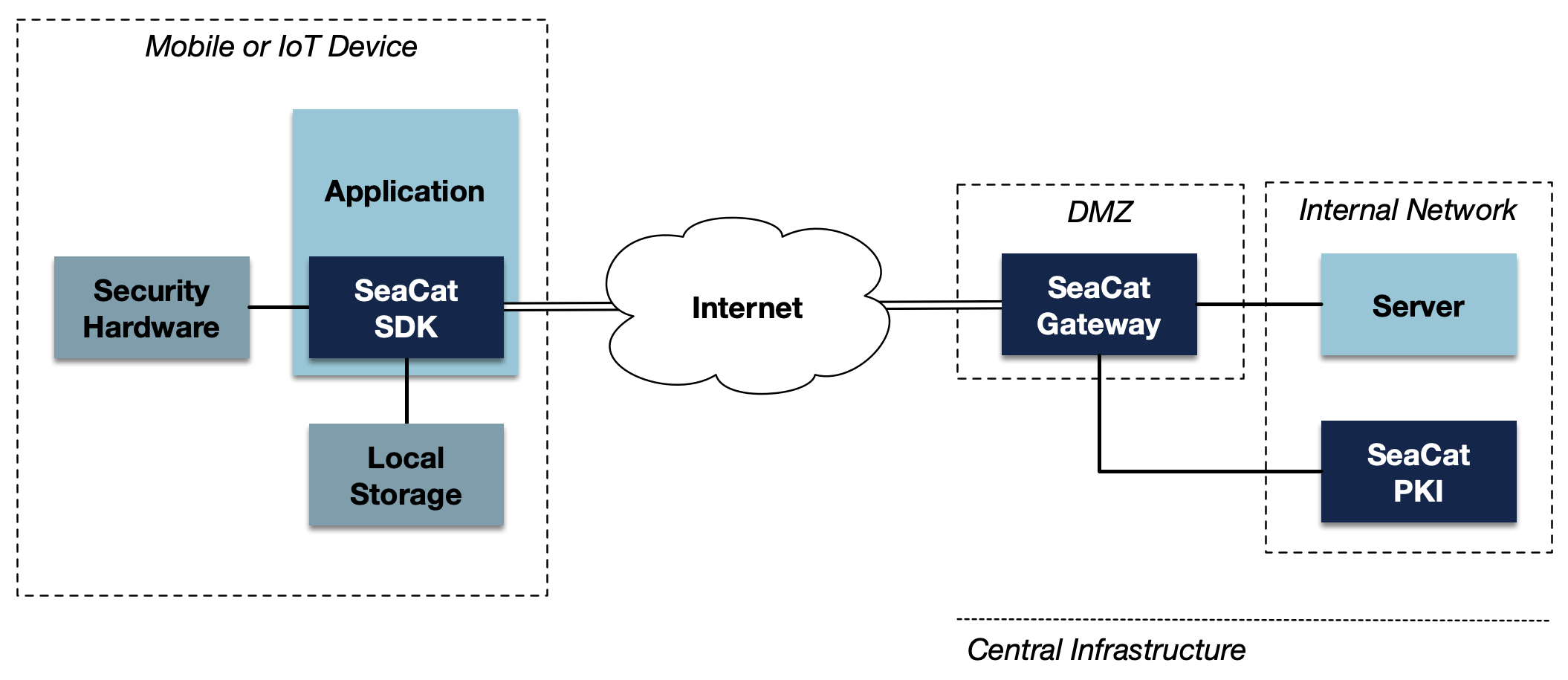
Strong cyber security
Build and operate the app free from any cyber-security incident. SeaCat is a cyber-security platform created by experts, and it features all cyber-security and data privacy must-haves.
Fast deployment
SeaCat deployment is smooth and hassle-free. SeaCat improves your security level instantly, with no need for custom development.
Seamless user experience
Cyber-security should not come at the cost of the user experience. SeaCat requires no pesky configurations or procedures on the part of the user; SeaCat employs all modern cyber-security features, such as biometrical authorization, and hardware security modules.