Companies that trust TeskaLabs




Security
TeskaLabs SIEM will bring a central overview of the entire company infrastructure and early detection helps eliminate risks and their possible effects on the operation of your company. TeskaLabs SIEM will always be one step ahead of potential threats and you will gain absolute supervision.
Compliance
TeskaLabs is cybersecurity expert and therefore all our products meet the security standards of your company. TeskaLabs SIEM ensures regulatory compliance with legislation covering Cyber Security, GDPR and ISO 27001:2013.
Speed and automation
Automated real-time detection and reporting of known incidents and anomalies will allow you to quickly react and prioritize the solution of individual incidents. Time savings allow you to proactively search for potential threats and enhance the flexibility of your IT infrastructure.
Main benefits
-
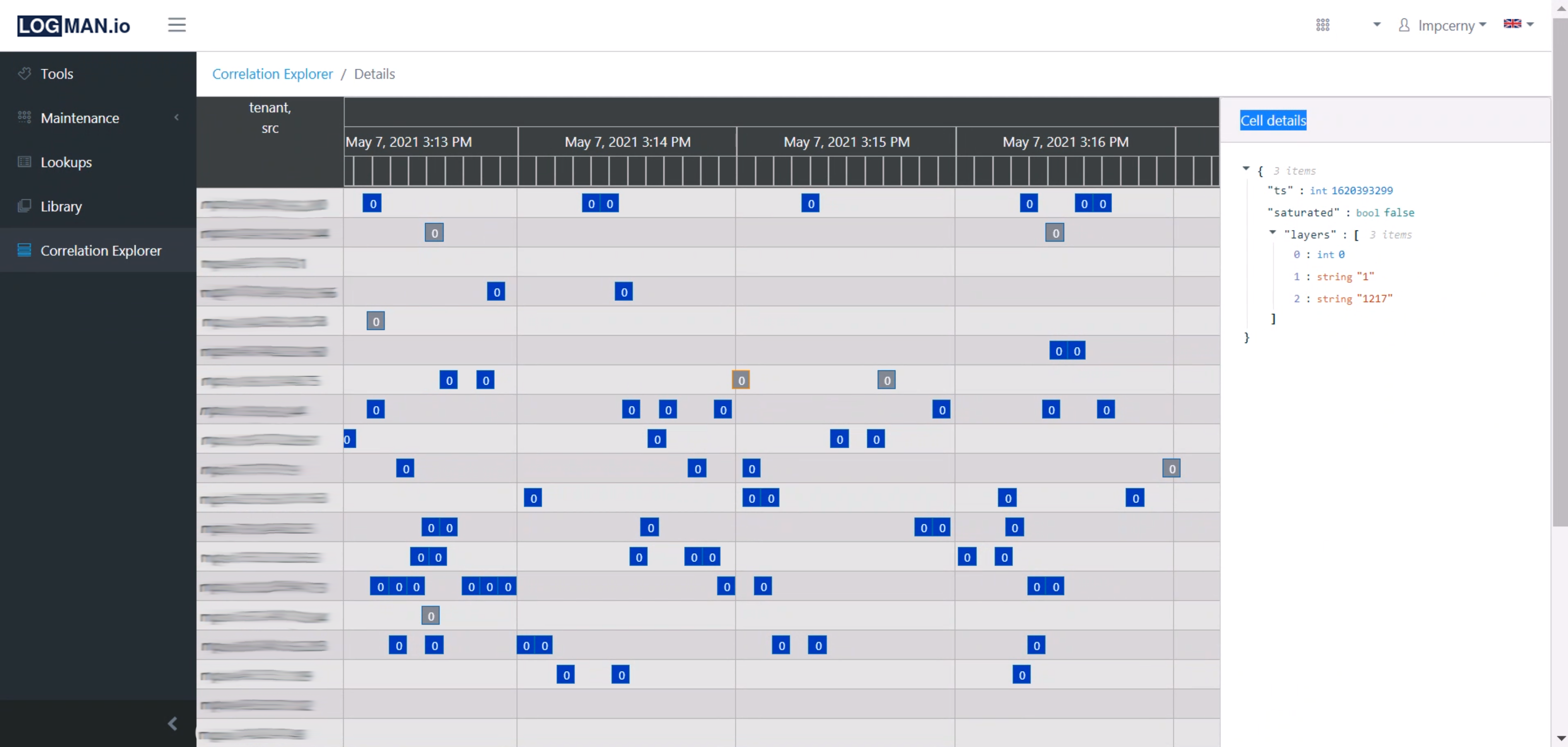
Overview of the events from different devices on time
-
More flexible and faster response to security incidents
-
Automatic correlations
-
Automatic event responses
-
Controlled data access
-
Optimization of IT security processes
-
Improved safety and risk management
-
Event recording for forensic analysis purposes
Key features
-
Real-time data processing stream
-
Unique solution of High availability (HA) - meets the ISO 27001:2013 requirements
-
Flexibility – microservices infrastructure supports development of new functions that can be easily deployed to existing functional units. The result is highly flexible system that can respond to changes and new security requirements.
-
Scalability – support of horizontal and vertical scaling
-
Web UI – elimination of multiple consoles
-
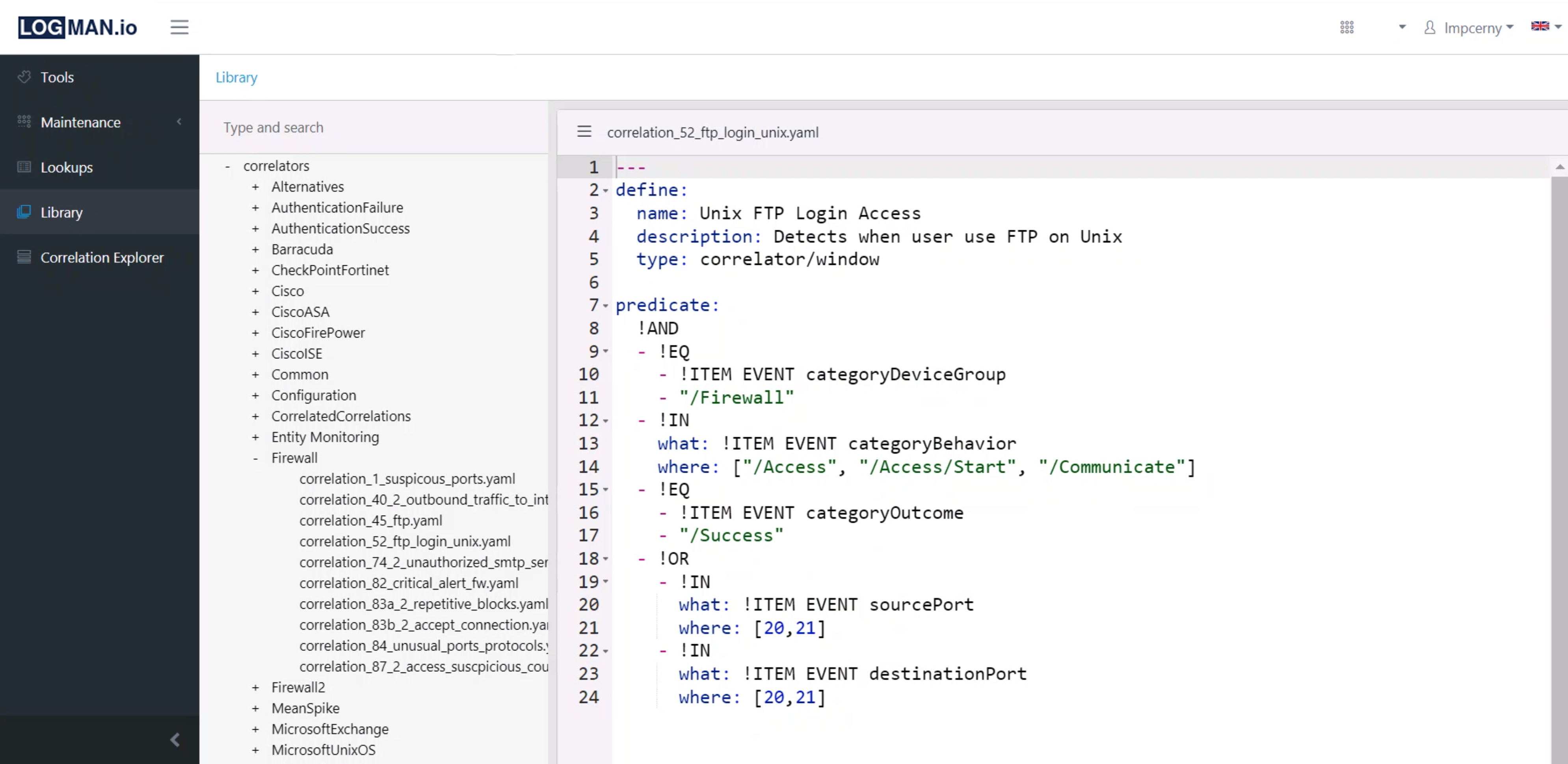
Forensic and reverse analysis of activities
-
Direct support of development team
-
Open platform - no Vendor lock-in
-
Easy extension to areas outside cybersecurity, ie. Construction of a real-time analytical platform for customer experience (CEM) and many more
-
Single Sign On (SSO), connectable with the company user database (LDAP)
-
Wide range of use for Business Intelligence, Big Data and Machine Learning
Technical parameters
-
Multi-tenancy
-
High level of permeability – permanent income of more than 100,000 EPS
-
Fully upgradable to active/active cluster with unlimited number of knots
-
Out of the box libraries and creation of your own detection rules without the need for programming
-
Scalable cluster by default
-
Unlimited disk storage
Deployment
Hardware appliance – delivery with the hardware
On premise – software license
Security Operation Center (SOC), MSSP (Managed Security Service Provider)
Virtual appliance – delivery in virtualized environment
Open platform




Supported devices
| Networking | Cisco, HP, Huawei, Aruba, Dell, 3C, Extreme Networks, Brocade SAN, Mikrotik |
|---|---|
| Firewalls | Fortinet, Juniper, Checkpoint, Kernum, Cisco ASA, Dell SonicWall, H3C, Hillstone, Sophos, Palo Alto Networks |
| Directory services | MS ActiveDirectory, Novell eDirectory |
| Databases | Oracle, MS SQL, MySQL, PostgreSQL, SAP |
| Windows servers, workstations, and applications | Hyper-V, DHCP, Firewall, IIS, Sharepoint, Exchange |
| Linux servers | Apache httpd, Tomcat, Nginx |
| Virtual servers | VMWare ESX, Vcenter, FlowMon |
| WiFi | FortiNet, Aruba, HP, Cisco, H3C, Trapeze / Juniper, UBNT, Dell, Ruckus |
| Antivirus | Avast, AVG, ESET, Kaspersky, Microsoft Defender |
Possible extension to other devices according to customer needs.
Technical documentation for TeskaLabs SIEM is available here.
Contact us
Leave your contact information and our specialist will contact you shortly.
We guarantee that your email and other personal information are confidential and will not be sold or rented.