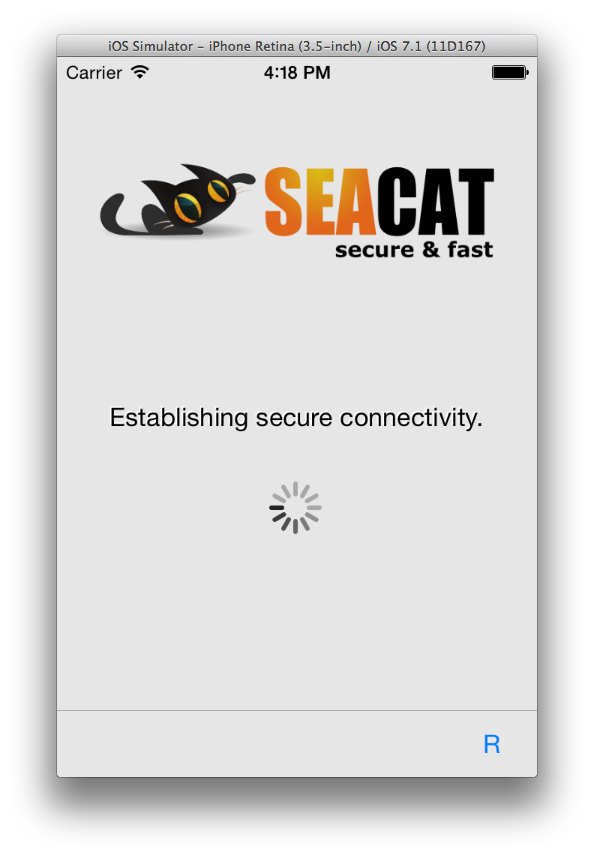
SeaCat trial
In order to help you to evaluate and use our product we have prepared an trial version that is freely available for download.
Trial version is limited to emulator/simulator only, you cannot use that on a real device. There is however no expiration date of a trial, so feel free to use it for any amount of time you need for the evaluation or even an actual development.
Please drop us an email about your SeaCat experience, you will help us to make product even better. Also, we will be more than happy to support you in your journey with SeaCat, so just tell us and we will gladly assist you.
iOS and Mac OS X
-
Download
By downloading this package you are accepting the SeaCat trial license. - SeaCat Tutorial series
SeaCat trial license
The SOFTWARE PRODUCT (SeaCat trial) is protected by copyright laws and international copyright treaties, as well as other intellectual property laws and treaties.
BY USING THE SOFTWARE PRODUCT, YOU ARE AGREEING ON BEHALF OF THE ENTITY USING THE SOFTWARE PRODUCT ("COMPANY") THAT COMPANY WILL BE BOUND BY AND IS BECOMING A PARTY TO THIS LICENSE AGREEMENT ("AGREEMENT") AND THAT YOU HAVE THE AUTHORITY TO BIND COMPANY. IF COMPANY DOES NOT AGREE TO ALL OF THE TERMS OF THIS AGREEMENT, DO NOT USE THE SOFTWARE PRODUCT. COMPANY HAS NOT BECOME A LICENSEE OF, AND IS NOT AUTHORIZED TO USE THE SOFTWARE PRODUCT UNLESS AND UNTIL IT HAS AGREED TO BE BOUND BY THESE TERMS.
Company may not use the SOFTWARE PRODUCT if Company is a direct competitor.
- LICENSES
SOFTWARE PRODUCT is licensed as follows:- Time span.
This license is granted for unlimited period of time. - Usage.
This license allows Company to use SOFTWARE PRODUCT on an emulator of mobile device. Use of the SOFTWARE PRODUCT on physical mobile device is explicitly prohibited. - Commercials.
The SOFTWARE PRODUCT can be used only for evaluation and software development and testing. Any other uses require written confirmation from TESKALABS LTD. Using SOFTWARE PRODUCT to generate profit is prohibited unless you are granted with written confirmation from TESKALABS LTD.
- Time span.
- DESCRIPTION OF OTHER RIGHTS AND LIMITATIONS
- Copyright Notices.
You must not remove or alter any copyright notices on any copy of the SOFTWARE PRODUCT. - Distribution.
You may not distribute or sell whole or any part of the SOFTWARE PRODUCT to third parties. License will be revoked if distributed or sold to third parties. - Rental.
You may not rent, lease, or lend the SOFTWARE PRODUCT. - Modification.
You are not allowed to modify the SOFTWARE PRODUCT in any way. License will be automatically revoked when the SOFTWARE PRODUCT is modified.
- Copyright Notices.
- COPYRIGHT
All title, including but not limited to copyrights, in and to SOFTWARE PRODUCT and any copies thereof are owned by TESKALABS LTD. - NO WARRANTIES
TESKALABS LTD expressly disclaims any warranty for the SOFTWARE PRODUCT, which is provided 'as is' without any express or implied warranty of any kind, including but not limited to any warranties of merchantability, non-infringement, or fitness of a particular purpose. - LIMITATION OF LIABILITY
In no event shall TESKALABS LTD be liable for any damages due to use of SOFTWARE PRODUCT, to the maximum extent permitted by law. This includes without limitation, lost profits, business interruption, or lost information. In no event will TESKALABS LTD be liable for loss of data or for indirect, special, incidental, consequential (including lost profit), or other damages. TESKALABS LTD shall have no liability with respect to the content of the SOFTWARE PRODUCT or any part thereof, including but not limited to errors or omissions contained therein, libel, trademark rights, business interruption, loss of privacy or the disclosure of confidential information.
Need a help?
Have a question we didn’t cover?
Do you have comments or feedback?
Feel free to contact me at johnny@teskalabs.com.
Most Recent Articles
You Might Be Interested in Reading These Articles

A beginner-friendly intro to the Correlator for effective cybersecurity detection
At TeskaLabs, we know that a cybersecurity system is only as effective as its ability to detect threats. That's why we developed a powerful tool that will prove essential in your arsenal: the Correlator.
Published on March 15, 2024
SeaCat Starter Pack for iOS
Starter pack is SeaCat distribution package that is prepared to enable quick evaluation and understanding how SeaCat product works. Also it is a boilerplate for new mobile applications that are equipped with SeaCat.
Published on April 02, 2015

What’s The Difference Between Seacat and VPN?
One of the most common questions people asked us is if SeaCat some kind of a VPN? It's not. Virtual Private Network (VPN) extends a private network across a public network, providing secure connectivity from/to a mobile device. Every application on this device, thus now has access to the private network through the channel opened by VPN. This is safe up to a certain level because it is almost impossible to ensure the integrity of every application on the devices. Especially now when there are apps for everything, and users can download them from Google Play and the Apple store.
Published on November 25, 2014