The Question That Everybody Asks: What’s The Difference Between Seacat and VPN?

One of the most common questions people asked us is “Is SeaCat some kind of a VPN?”
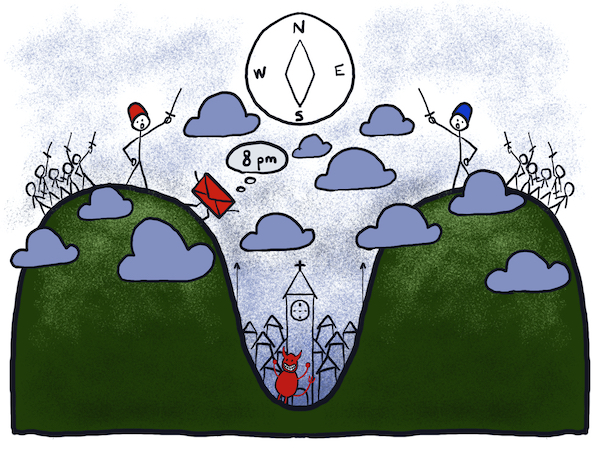
Well it’s not. Virtual Private Network (VPN) extends a private network across a public network, providing secure connectivity from/to a mobile device. Every application on this device, thus now has access to the private network through the channel opened by VPN. This is safe up to a certain level because it is almost impossible to ensure the integrity of every application on the devices. Especially now when there are apps for everything, and users can download them from Google Play and the Apple store.
Recent research from Arxan shows that 97% of the top 100 paid apps on the Google Android platform and 87% of the top 100 paid apps for Apple iOS had been hacked. Does it seem like almost every app has been hacked? As you can see, your data are not secured using applications from bespoke sources. Data being sent to and from your mobile application are easily stolen and used in a harmful way to you and your organisations.
One common hack we often hear about comes from the form of malware. What if you have them in your mobile devices? These malware apps would then, through the VPN channel you have opened, exploit the data residing on servers of your private network. For this precise reason that Gartner’s Janessa Rivera proposes “new models of building security directly into applications; every app needs to be self-aware and self-protecting.”
On the other hand, Seacat is a Mobile Secure Gateway (MSG) providing secure connectivity directly from the mobile application to the gateway entry to the DMZ before allowing any further activity to the sensitive data centre of your organisation. Because of the required mutual authentication, only application with trustable certificates are allowed to access the private network. This is the reason MSG narrows the attack vector to the minimum and keep your data as safe as possible.
Is SeaCat still a VPN? You tell us.
Most Recent Articles
You Might Be Interested in Reading These Articles
Entangled ways of product development in the area of cybersecurity #3 - LogMan.io
At that time I lived in Prague for a short time, which is not a very friendly place to live, but it allowed me to go to the office almost every day. A bigger surprise awaited Vlaďka and Aleš when I told them that I was going to move to a house almost eighty kilometres from the office and that I would need to be mainly at the home office.
Published on January 15, 2023
Entangled ways of product development in the area of cybersecurity #2 - BitSwan
After successfully completing my engineering degree, I finally started working full-time at TeskaLabs just as I initially promised. In addition to data from the world of telecommunications, we started to learn data from the world of logistics in BitSwan, which of course required being able to calculate the cost of transporting some cargo from point A to point B.
Published on December 15, 2022
From State Machine to Stateless Microservice
In my last blog post, I wrote about implementing a state machine inside a microservice I call Remote Control that will automate deployments of our products and monitor the cluster. Here I would like to describe how all this was wrong and why I had to rewrite the code completely.
Published on February 15, 2023