SeaCat Performance Test
We decided to perform this test to validate our architectural, design and implementation decisions in regards to SeaCat performance. Our goal was to build the best-in-class product using the most advanced techniques to deliver highest possible throughput yet not compromising the security of the communication in any way. Results of the test have been fed back into our development team to improve further overall performance characteristics of the solution.
We want to illustrate SeaCat's performance related to HTTP and HTTPS protocols. SeaCat provides speed that is close to HTTP and the level of security that is at least equal to HTTPS. If performance is important to you, you will be able to put all three methods in some perspective.
Measured numbers should help you in deciding about your environment sizings.
Test configuration
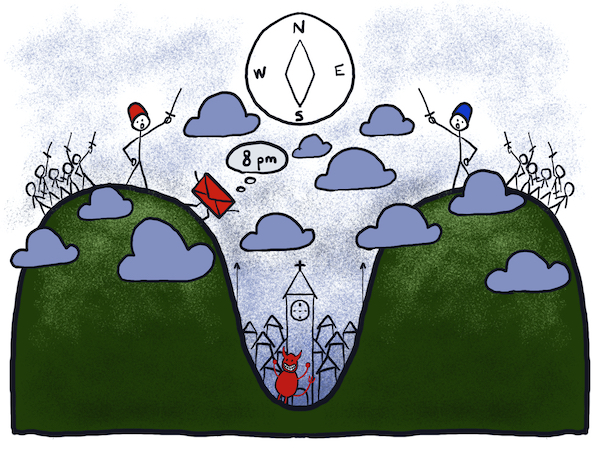
The test environment has been configured using the following architectural recommendations (see bellow PDI diagram). We build it using Amazon AWS EC2 service.

The test based on launching GET request that retrieves a certain XML file from the HTTP host. This cycle of request and response is called transaction for the sake of this test.
We build custom performance tool for SeaCat, modelled after well-known ab tool from HTTP Apache server suite. ab tool is also used for reference testing of HTTP and HTTPS which is configured in the same way (or as much as possible).
We crafted 128 B, 512 B, 1 KiB, 2 KiB XML, 4 KiB, 8 KiB and 16 KiB XML files that are served by HTTP hosts during the test.
Further details of test configuration are attached at the end of this article.
Results
c3.xlarge (4 vCPU cores)

| HTTP | HTTPS | SeaCat | |
|---|---|---|---|
| 128 B XML | 9634 | 869 | 13685 |
| 512 B XML | 9724 | 868 | 13766 |
| 1 KiB XML | 9492 | 860 | 14186 |
| 2 KiB XML | 9554 | 866 | 13364 |
| 4 KiB XML | 9469 | 859 | 11882 |
| 8 KiB XML | 8876 | 850 | 10353 |
| 16 KiB XML | 6054 | 831 | 5457 |
Numbers are in transactions per second.
c3.large (2 vCPU cores)

| HTTP | HTTPS | SeaCat | |
|---|---|---|---|
| 128 B XML | 8111 | 511 | 8269 |
| 512 B XML | 8406 | 511 | 8271 |
| 1 KiB XML | 8932 | 512 | 8116 |
| 2 KiB XML | 8376 | 512 | 7859 |
| 4 KiB XML | 8407 | 511 | 7342 |
| 8 KiB XML | 8291 | 510 | 6614 |
| 16 KiB XML | 6249 | 508 | 3836 |
Numbers are in transactions per second.
Detailed information
SeaCat Gateway
- Version: 14.03 (trial)
- Number of child processes: (2 * number of CPU cores) + 2
- Memory is non-critical: <500kb was used during the test
- Number of open files (
ulimit -n) has to be set reasonably high (e.g. 8192)
NGINX host servers
- Version: 1.4.6
- Number of workers (
worker_processes): 32
Client test box
- Custom build performance test client for SeaCat
- 'ab' tool (from HTTP Apache toolbox) for HTTP and HTTPS reference test
$ ab -c8 -n100000 http://ip-...eu-west-1.compute.internal/1k.xml$ ab -c8 -n10000 https://ip-....eu-west-1.compute.internal/1k.xml
Cryptography configuration of SeaCat and HTTPS
- Protocol: TLSv1.2
- Cypher: ECDHE-RSA-AES128-GCM-SHA256 (2048 bit RSA, 128 bit AES)
- No client/server certificate trust validation
Amazon AWS details
- Ubuntu Server 14.04 LTS (PV), SSD Volume Type - ami-e90dc49e (64-bit)
- Root device type: ebs
- Virtualization type: paravirtual
- Dedicated placement group (cluster)
- eu-west-1c
c3.large
- High Frequency Intel Xeon E5-2680 v2 (Ivy Bridge) Processors
- vCPU: 2
- RAM: 3.75G
- AES-NI present
c3.xlarge
- High Frequency Intel Xeon E5-2680 v2 (Ivy Bridge) Processors
- vCPU: 4
- RAM: 7.5G
- AES-NI present
c3.2xlarge
- High Frequency Intel Xeon E5-2680 v2 (Ivy Bridge) Processors
- vCPU: 8
- RAM: 15G
- AES-NI present
c3.8xlarge
- High Frequency Intel Xeon E5-2680 v2 (Ivy Bridge) Processors
- vCPU: 32
- RAM: 60G
- AES-NI present
Do you have a question?
Have a question we didn’t cover? Please feel free to contact us.
Most Recent Articles
You Might Be Interested in Reading These Articles
From State Machine to Stateless Microservice
In my last blog post, I wrote about implementing a state machine inside a microservice I call Remote Control that will automate deployments of our products and monitor the cluster. Here I would like to describe how all this was wrong and why I had to rewrite the code completely.
Published on February 15, 2023
SeaCat tutorial - Chapter 2: Simple Post (iOS)
The goal of this article is to create a simple iOS client which generates a simple POST Request which will be read in host written in Node.js and the output generated in the console. The whole comunication will be handled by SeaCat which help us to establish fast and secure connection among our key components.
Published on September 09, 2014

SeaCat tutorial - Chapter 3: Introduction to REST Integration (iOS)
The goal of this article is to extend the knowledge and develop an iOS application which is able to comunicate with REST interface provided by Node.js that we are going to create as well. A full integration with SeaCat is essential for information security of our example.
Published on October 07, 2014
