SeaCat Technology and the Latest OpenSSL Update (1.1.0e)
February 21, 2017
OpenSSL released a new version on February 16, 2017. The new version fixed one high-severity issue regarding renegotiation of the Encrypt-then-MAC (EtM) extension, an approach to authenticated encryption. The vulnerability is identified as CVE-2017-3733. Several, not yet known, cipher suites are affected; therefore disabling affected cipher suites can not be used as a workaround.
TeskaLabs’ SeaCat technology uses the 1.0.2 series for its cryptography library, so this update does not affect our technology in any way.
Recommendation:
Your systems and applications are affected if they use OpenSSL 1.1.0 series. EtM is the strongest approach to authenticated encryption. We strongly recommend you to update to the latest version.
Your application developers or operators should inform you about update requirements. If you have any concern about the security of your systems, we are ready to help you.
If you have any question, please contact support@teskalabs.com. Alternatively, look at our documentation to know more about SeaCat application security technology.
Most Recent Articles
You Might Be Interested in Reading These Articles
SeaCat Technology and the Latest OpenSSL Update (1.1.0d, 1.0.2k)
We help you to operate your mobile and IoT apps securely. You may have noticed that OpenSSL released a new version on 26 January 2017. The new release fixed one low-severity issue and three moderate ones.
Published on January 26, 2017
SeaCat Application Security Technology Is Not Impacted by the Dirty Cow Issue (CVE-2016-5195)
The new vulnerability, DirtyCOW, (CVE-2016-5195) exploits a flaw in private read-only memory mappings. However, this critical impact vulnerability has existed in Linux for nine years and only got discovered recently.
Published on October 25, 2016
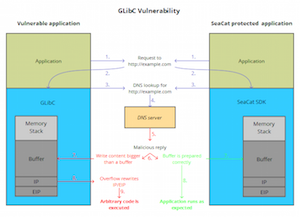
TeskaLabs’ Technology SeaCat Unaffected by GNU C Library Security Vulnerability (CVE-2015-7547)
TeskaLabs, a Prague and London based startup in application security, today affirmed that their core products are not exposed to the GLibC flaw, a highly critical security vulnerability. There is now a rapidly growing number of IoT devices that use Linux as their operating system and inherently GLibC.
Published on February 17, 2016