Cybersecurity - Data Privacy - IT Trends - Innovations
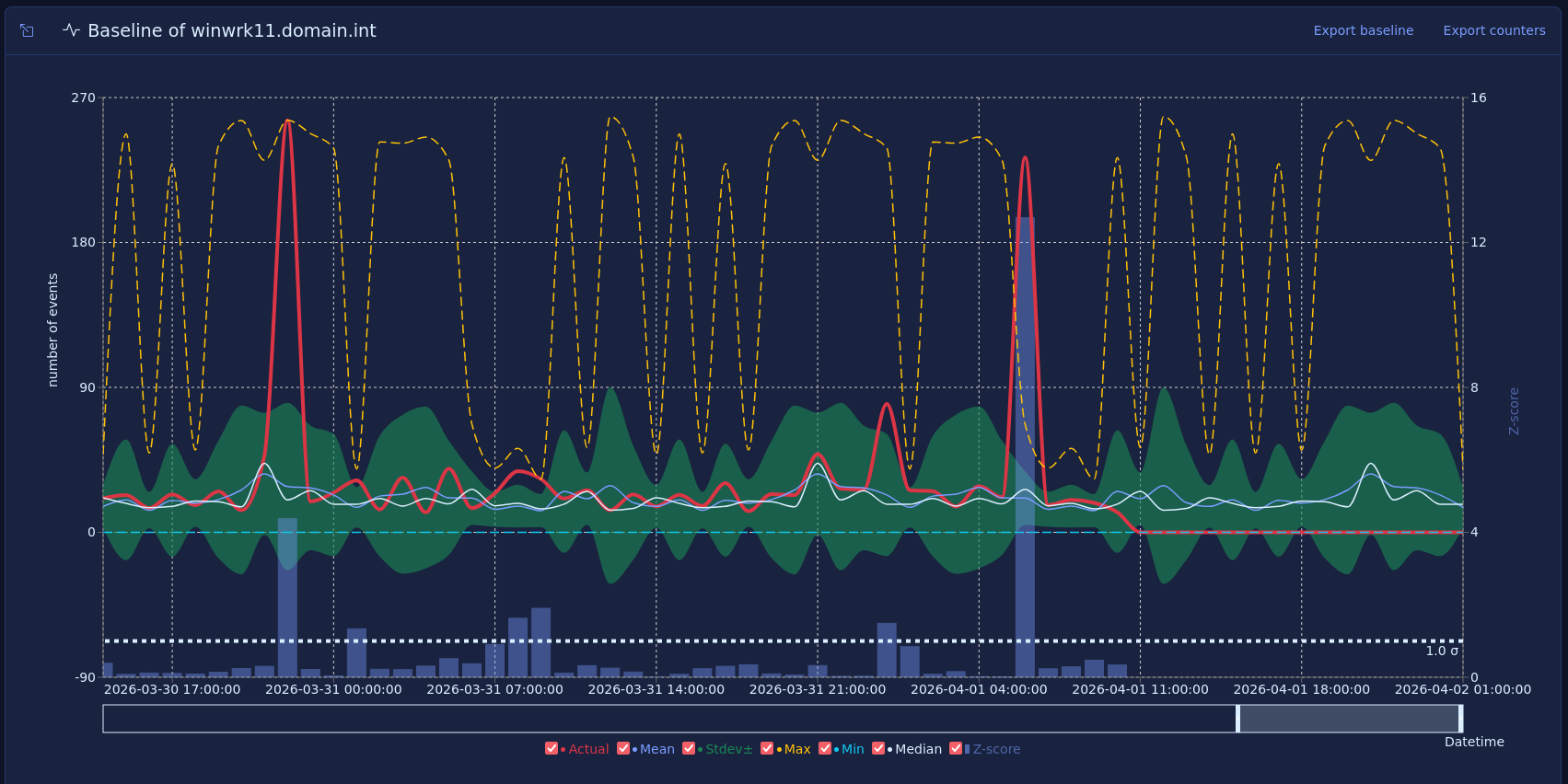
Vector baselines and host behavior
Most security monitoring focuses on what happened, such as a failed login, a new admin, or a suspicious process. That approach is useful, but many strong warning signs do not come from one event. They come from a change in how a host behaves over time.
Published on March 16, 2026