
Personal Data Deindetification: Anonymization
If you manage private data of any kind, you need to be familiar with the process of anonymization and how it can be used to keep the information you store safe from data breaches.
What Is It?
Anonymization translates into the irreversible removal of information that could lead to a person being identified in combination with other information or on the basis of the removed information itself.
Anonymized data, in order to be truly anonymized, must be stripped of all identifiable information. This makes it impossible to derive insights into a specific individual, even by your own company who handles the anonymization.
Considerations
If a person sends a file to a company, there may be information within that file that can be traced back to them. However, if the file is anonymized, all the associated personal data will not be traceable back to the sender--or so goes the theory.
With data anonymization, the original field layout of the data (position, size, data type) will not be taken away, which means the data will still look realistic within a data environment.
However, through the process of de-anonymizing, the process can be reversed. Most of the anonymization techniques in use today can be bypassed. A person can reveal the personally-identifying information that was stripped away, like by cross referencing the stripped file with sets of records that are still visible.
In fact, it was in 2000 that a research breakthrough was made to show that the power of anonymization isn’t as powerful as many people are initally led to believe. This study revealed that about 87% of Americans can be uniquely identified with just three pieces of information that aren’t usually considered “personal”--especially not when taken out of the context of a personal file.
These three pieces of information are: sex, birthday, and ZIP code. Information that often isn’t anonymized during this process. And, even if it is, computer scienties in recent years have shown that just about any piece of data can be considered “personal” when combined with other relevant data pieces.
Ensuring Its Effectiveness
Anonymization is just one of many personal de-identification techniques that can be utilized for your business. When approached correctly, anonymization might be the right choice for a given data set. That decision, however, will rely on the information you are trying to secure and its sensitivity.
If you take all considerations into account, anonymization might be the right way forward, but there are some additional tips to help make it more effective. Doing so really requires your business to consider all of the information you are storing, determining what you really need to keep, and then delving into the surprisingly difficult question of: what really makes for personally identifiable data?
As multiple research studies have proven in recent years, the category of personal identifiable information (PII) is expanding as companies begin easily collecting more and more data points. With all that data online, it becomes that much easier to use the cross-referencing techniques and match a few data points up with the profile of an entire individual.
Picking a Method
In reality, your business cannot assume that anoymization processes can completely secure your consumers’ personal information. While it may be a method you employ, you are likely going to utilize it alongside many other methods for your business’ data base.
These other methods will be covered in this series, allowing you to learn more about each technique and decide which one is best fitted to your business’ specific needs. Additionally, if you happen to have questions or concerns, you shouldn’t hesitate to reach out to a professional.
References
- https://arstechnica.com/tech-policy/2009/09/your-secrets-live-online-in-databases-of-ruin/
Most Recent Articles
You Might Be Interested in Reading These Articles
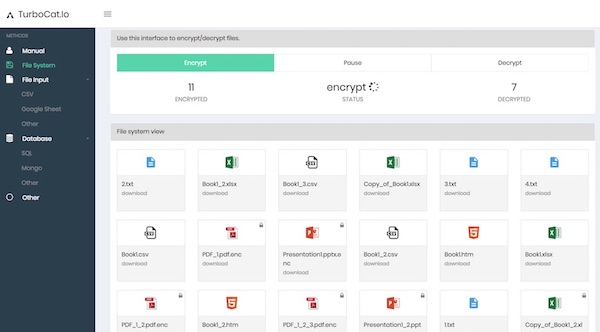
Customer interview: Read how Prodvinalco uses TurboCat.io for a file encryption
Data encryption is a critical part of GDPR compliance although there are no explicit GDPR encryption requirements. The regulation vaguely states that businesses must enforce safeguards and security measures to protect all consumer data that they handle. The GDPR refers to pseudonymization and encryption as “appropriate technical and organizational measures.
Published on September 13, 2018

Creative Dock, TeskaLabs, Indermedica, Czech Ministry of Industry and Trade and Line 1212 launch the indicative test for new COVID-19 coronavirus
🇨🇿 Uchránit přetížené zdravotníky před zbytečným náporem lidí i pomoci lidem, kteří mají obavy z nového typu koronaviru, ve správném vyhodnocení symptomů a dalším postupu má nový online Indikativní test Covid-19, který vyvinuly české technologické firmy spolu s ministerstvem průmyslu a obchodu a linkou 1212.
healthcare
data-privacy
covid19
Published on March 29, 2020

Developing a Mobile App in Healthcare
MediCat is one of TeskaLabs newest innovations and it centers around data protection and cybersecurity for the healthcare industry. In this article, we’ll explore the many use cases of MediCat.
medicat
data-privacy
healthcare
Published on October 15, 2018
